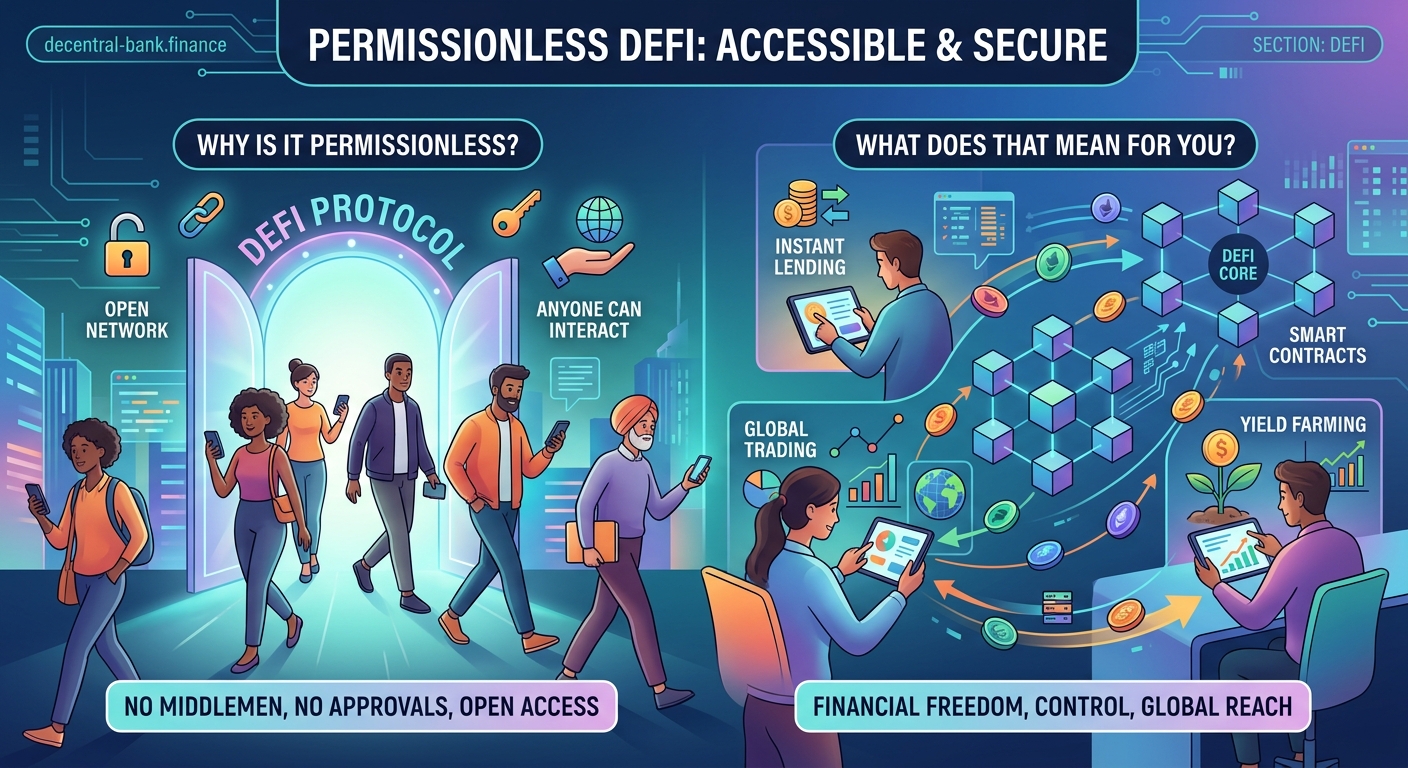
You’ve probably heard that DeFi is “permissionless,” but what does that actually mean for you? Unlike traditional banks that decide who gets an account, loan, or investment opportunity, permissionless systems let anyone participate. No credit check. No application. No waiting for approval. You just need a wallet and an internet connection.
Permissionless means DeFi protocols are open to everyone without requiring approval from banks or institutions. Anyone with a crypto wallet can lend, borrow, trade, or earn interest regardless of their location, credit history, or financial background. This openness creates both unprecedented access and new risks you need to understand before participating.
Breaking down permissionless access in simple terms
Permissionless doesn’t mean lawless or unregulated in the traditional sense. It means the protocol itself doesn’t gatekeep who can use it.
Think about opening a bank account. You fill out forms. You provide ID. You wait for approval. The bank reviews your credit history, employment status, and sometimes your nationality. They can reject you for dozens of reasons.
Now compare that to using a DeFi protocol. You connect your wallet. You interact with smart contracts. That’s it. The code doesn’t care about your credit score, where you live, or how much money you already have.
This fundamental difference is what makes DeFi permissionless. The system operates based on code, not human gatekeepers making subjective decisions about who deserves access.
Why traditional finance needs permission
Traditional financial systems built permission requirements for specific reasons. Banks need to comply with regulations. They want to avoid fraud. They need to assess risk before lending money.
These permission layers serve important purposes, but they also exclude billions of people. No permanent address? No bank account. Poor credit history from medical bills? No loan. Live in the wrong country? No access to certain investment products.
Each permission layer adds friction. Account opening takes days or weeks. International transfers cost significant fees. Investment minimums exclude people with less capital.
Traditional finance vs DeFi: understanding the key differences shows how these systems diverge at a fundamental level.
How DeFi protocols eliminate permission requirements
DeFi protocols replace human gatekeepers with smart contracts. These are self-executing programs that run exactly as coded.
When you want to borrow crypto, the smart contract checks one thing: do you have enough collateral? It doesn’t check your employment history. It doesn’t care about your age or nationality. It just verifies the math.
Here’s what happens when you interact with a permissionless lending protocol:
- You connect your wallet to the protocol interface
- You deposit collateral (usually crypto assets worth more than what you want to borrow)
- The smart contract automatically calculates how much you can borrow based on predetermined ratios
- You receive the borrowed funds instantly if you meet the collateral requirements
No application. No approval process. No waiting period.
The same permissionless access applies to trading on decentralized exchanges, providing liquidity to pools, or earning interest on deposits. The code treats everyone identically.
Real examples of permissionless access in action

A developer in Nigeria can provide liquidity to the same pool as a retiree in Japan. They both earn the same percentage of trading fees. Neither needed permission to participate.
A student in Argentina can borrow stablecoins against their crypto holdings at 2 AM on a Sunday. No bank would process that request, but the smart contract executes it immediately.
Someone who was denied a bank account due to poor credit can still earn interest on stablecoins through DeFi lending protocols. The protocol doesn’t check credit scores.
These aren’t hypothetical scenarios. Millions of people use permissionless protocols daily for exactly these reasons.
How does DeFi actually work without banks or middlemen? explains the technical mechanisms that make this possible.
What permissionless doesn’t mean
Permissionless access doesn’t mean consequence-free. Smart contracts still enforce rules. If your collateral value drops below required levels, you get liquidated automatically.
It doesn’t mean anonymous. Most blockchain transactions are publicly visible. Your wallet address appears on-chain, even if it’s not directly linked to your identity.
It doesn’t mean unregulated in all jurisdictions. Some countries restrict crypto access through internet service provider blocks or banking restrictions, even though the protocols themselves remain permissionless.
And critically, it doesn’t mean safe. Permissionless systems let anyone deploy smart contracts, including scammers. You need to verify what you’re interacting with.
The technical foundation of permissionless systems
Blockchain technology makes permissionless access possible. These distributed networks don’t have a central authority that can approve or deny access.
Smart contracts deployed on these blockchains inherit this permissionless nature. Once deployed, they run autonomously. No one can stop you from calling a function if you meet the coded requirements.
This creates interesting dynamics. A protocol developer can’t freeze your funds or deny you access, even if they wanted to. The code is the only authority.
Some protocols add administrative functions that let developers pause contracts in emergencies, but truly permissionless protocols avoid these mechanisms entirely.
Comparing permissionless and permissioned systems
| Feature | Permissionless DeFi | Traditional Finance |
|---|---|---|
| Account opening | Instant with any wallet | Days to weeks with approval |
| Access requirements | Wallet and funds | ID, credit check, address verification |
| Geographic restrictions | None at protocol level | Extensive based on regulations |
| Minimum balances | Usually none | Often required for accounts |
| Operating hours | 24/7/365 | Business hours only |
| Approval for transactions | Automatic via code | Manual review for large amounts |
The table shows clear differences, but permissionless systems aren’t automatically better for every use case. They trade institutional protections for open access.
Common misconceptions about permissionless access
Many people assume permissionless means anyone can do anything without consequences. That’s not accurate.
Smart contracts enforce strict rules. Try to borrow more than your collateral allows? The transaction fails. Try to withdraw from a staking contract before the lock period ends? The code prevents it.
Another misconception: permissionless systems have no accountability. Actually, blockchain’s transparency creates a permanent record of every transaction. This public ledger provides accountability, just through different mechanisms than traditional systems.
Some think permissionless access makes DeFi illegal. Permissionless protocols exist in a complex regulatory environment, but using open-source code generally isn’t illegal. Regulatory concerns focus more on specific activities, token classifications, and service providers.
The wallet is your permission slip
In permissionless DeFi, your wallet serves as your universal access credential. It’s not tied to your identity, credit history, or location. It’s simply a cryptographic key pair that proves you control certain assets.
This creates both opportunity and responsibility. You don’t need anyone’s permission to create a wallet, but you also can’t call customer service if you lose your seed phrase.
5 critical mistakes beginners make when setting up their first DeFi wallet covers essential security practices for managing this responsibility.
Your wallet connects to any permissionless protocol. Same wallet, different protocols. You’re not creating separate accounts or going through multiple approval processes.
Security implications of permissionless systems
Permissionless access creates unique security challenges. Since anyone can deploy smart contracts, malicious actors can create fake protocols that look legitimate.
You need to verify what you’re interacting with. Check contract addresses. Read audit reports. Use established interfaces. The burden of due diligence falls on you.
Traditional banks protect you from many scams through their permission layers. They verify merchants. They can reverse fraudulent transactions. They monitor for suspicious activity.
Permissionless systems offer none of these protections. Transactions are irreversible. No one can recover funds sent to a scam contract. You are your own security department.
The permissionless nature of DeFi means you have complete control over your assets, but that control comes with complete responsibility. There’s no customer service number to call if you make a mistake or fall for a scam. Verify everything before you interact with any protocol.
The complete DeFi security checklist for beginners provides a systematic approach to staying safe.
Who benefits most from permissionless access
People excluded from traditional finance benefit enormously. This includes:
- Individuals in countries with unstable banking systems
- People without credit history who can’t access loans
- Workers who need to send money internationally without high fees
- Investors locked out of opportunities due to geographic restrictions
- Anyone who values financial privacy and control
But permissionless access also benefits people with full access to traditional finance. You might use both systems for different purposes. Banks for insured deposits and regulated services. DeFi for higher yields, 24/7 access, or specific financial tools unavailable elsewhere.
The ability to participate without permission doesn’t mean you must abandon all traditional financial services. Many people use hybrid approaches.
Risks unique to permissionless environments
Smart contract bugs affect everyone equally. A vulnerability doesn’t discriminate based on who’s using the protocol. If the code has a flaw, all users face the same risk.
No insurance or deposit protection exists in most permissionless protocols. Traditional banks offer FDIC insurance up to certain amounts. Permissionless protocols typically offer nothing similar.
Market manipulation can occur more easily in smaller permissionless markets. Without regulatory oversight, pump-and-dump schemes and other manipulation tactics face fewer barriers.
Why DeFi yields are high and what risks you’re actually taking examines the risk-reward tradeoffs in detail.
Liquidity can vanish suddenly. In traditional finance, market makers and regulations provide some stability. Permissionless protocols have no such requirements.
How to start using permissionless protocols safely
Start with established protocols that have been battle-tested. Uniswap, Aave, and Compound have processed billions in transactions and survived multiple market cycles.
Begin with small amounts. Test the process before committing significant funds. Permissionless access means you can experiment with minimal investment.
Use multiple sources to verify protocol information. Check official documentation, community forums, and independent security audits. Don’t rely on a single source.
Steps for safe first interactions:
- Research the protocol thoroughly using multiple independent sources
- Verify the official contract address on the project’s website and blockchain explorer
- Start with a small test transaction to understand the process
- Monitor your first transaction closely to ensure it behaves as expected
- Gradually increase your involvement as you gain confidence and understanding
Getting started with DeFi: your complete beginner roadmap walks through this process step by step.
The role of governance in permissionless systems
Many permissionless protocols include governance mechanisms. Token holders can propose and vote on changes to protocol parameters.
This creates an interesting dynamic. The protocol remains permissionless for users, but the community collectively decides how it evolves.
Governance participation is also permissionless. Anyone holding governance tokens can vote, regardless of their background or status. A small holder has voting power proportional to their tokens, just like a large holder.
5 ways governance tokens actually give you control over DeFi protocols explains how this participation works in practice.
Some argue that large token holders dominate governance, creating a new form of gatekeeping. Others counter that token-weighted voting aligns incentives with protocol success.
Common mistakes when using permissionless protocols
Assuming all protocols are equally safe because they’re all permissionless. Quality varies dramatically. Some protocols undergo rigorous audits and testing. Others deploy untested code.
Ignoring gas fees when making small transactions. Permissionless access doesn’t mean free access. Network fees can exceed the value of small transactions, especially during network congestion.
Failing to research before approving token contracts. When you approve a contract to spend your tokens, you’re granting permission at the smart contract level. Malicious contracts can drain approved tokens.
Not understanding liquidation risks when borrowing. Permissionless lending protocols liquidate positions automatically when collateral drops below required ratios. No warnings. No grace periods.
Using protocols you don’t understand. Permissionless access makes participation easy, but that doesn’t mean you should use complex protocols without understanding how they work.
Permissionless protocols and regulatory uncertainty
Regulators worldwide are still figuring out how to approach permissionless systems. These protocols don’t fit neatly into existing regulatory frameworks.
Some jurisdictions focus on regulating access points like exchanges and wallet providers rather than protocols themselves. Others attempt to regulate the protocols or their developers.
This uncertainty creates risk. A protocol that’s permissionless today might face regulatory pressure tomorrow. Developers might add compliance features that reduce permissionless access.
Users should stay informed about regulatory developments in their jurisdiction. Permissionless at the protocol level doesn’t guarantee legal access everywhere.
The future of permissionless finance
Permissionless systems continue evolving. Layer 2 solutions make access cheaper. Cross-chain bridges expand options. New protocols experiment with different approaches to balancing openness and safety.
Some projects explore “permissioned permissionless” models. The protocol remains open, but certain features require identity verification or compliance checks. This hybrid approach attempts to combine regulatory compliance with broad access.
Others double down on pure permissionless design, viewing any gatekeeping as antithetical to DeFi’s core principles.
The tension between these approaches will likely shape DeFi’s development for years.
Making sense of permissionless access for your situation
Permissionless doesn’t automatically mean better. It means different tradeoffs.
You gain access without approval, but lose institutional protections. You get 24/7 availability, but accept full responsibility for security. You can participate from anywhere, but face regulatory uncertainty.
For some people in some situations, these tradeoffs strongly favor permissionless systems. For others, traditional finance remains more appropriate.
The key is understanding what permissionless actually means, so you can make informed decisions about when and how to participate. Access without permission is powerful, but it’s not without risks or responsibilities.
7 common DeFi terms every beginner should know before getting started helps build the broader vocabulary you need to navigate this space confidently.
Your next steps with permissionless protocols
Now you understand what permissionless means in DeFi. It’s not just a buzzword. It’s a fundamental architectural choice that creates both opportunities and challenges.
Start small. Choose established protocols. Verify everything. Take responsibility for your security. And remember that permissionless access is a tool, not a guarantee of success or safety. How you use that tool determines your outcomes in this open financial system.




