You paid $50,000 for a comprehensive smart contract audit. The report came back clean with only minor suggestions. Three weeks after launch, a hacker drained $2 million from your protocol through a reentrancy attack the auditors never flagged.
This scenario plays out repeatedly across DeFi. Audited protocols get exploited. Users lose funds. Teams scramble to explain how security firms missed obvious vulnerabilities.
The uncomfortable truth is that audits are not bulletproof. They catch many bugs, but critical vulnerabilities slip through with alarming frequency.
Smart contract audits fail because of time constraints, scope limitations, human error, and the complexity of modern protocols. Auditors review code snapshots, not live integrations. They miss business logic flaws, economic attacks, and edge cases. A clean audit report does not guarantee security. Projects need multiple audits, formal verification, bug bounties, and continuous monitoring to protect users from critical vulnerabilities.
Time pressure creates blind spots
Audit firms operate under tight deadlines. Most audits run for two to four weeks regardless of protocol complexity.
A lending protocol with 5,000 lines of code gets the same timeline as a simpler token contract. Auditors must balance thoroughness with delivery schedules.
When time runs short, teams prioritize known vulnerability patterns. They check for reentrancy, integer overflow, and access control issues. But novel attack vectors require deeper analysis that deadlines don’t allow.
Projects often change code during the audit period. Teams fix bugs, add features, or refactor functions. Each change requires re-review, but the deadline stays fixed. Auditors mark sections as “not reviewed” or “partially reviewed” in final reports.
These time-stamped snapshots create a false sense of security. The code that gets deployed often differs from what auditors examined.
Scope limitations leave dangerous gaps
Audit agreements define specific boundaries. Auditors review the contracts listed in the scope document. Nothing more.
Your protocol might integrate with five external protocols. The audit covers your code but not how it interacts with Uniswap, Aave, or Chainlink oracles. Those integration points become attack surfaces.
Business logic vulnerabilities fall outside traditional security reviews. An auditor confirms your liquidation function executes correctly but doesn’t evaluate whether your liquidation threshold makes economic sense.
Understanding how DeFi protocols work helps you recognize these gaps. The code might be secure while the economic model invites manipulation.
Governance mechanisms rarely get adequate scrutiny. Your DAO controls critical parameters, but auditors focus on technical exploits, not governance attacks. A malicious proposal could drain the treasury through perfectly functioning code.
Auditors are human and make mistakes
Security researchers are not infallible. They miss things. They misunderstand complex logic. They make incorrect assumptions about how functions interact.
Auditing requires intense concentration over long periods. Mental fatigue sets in. A reviewer might catch 95% of issues in the first week but miss critical bugs in week three.
Different auditors have different expertise. One excels at finding reentrancy bugs. Another specializes in economic attacks. No single auditor masters every attack vector.
Audit firms assign multiple reviewers to each project, but coordination problems emerge. One auditor assumes another checked a specific function. Both skip it.
The most dangerous vulnerabilities often hide in plain sight. Auditors see thousands of lines of code and develop pattern blindness. They spot complex exploits but miss simple logic errors.
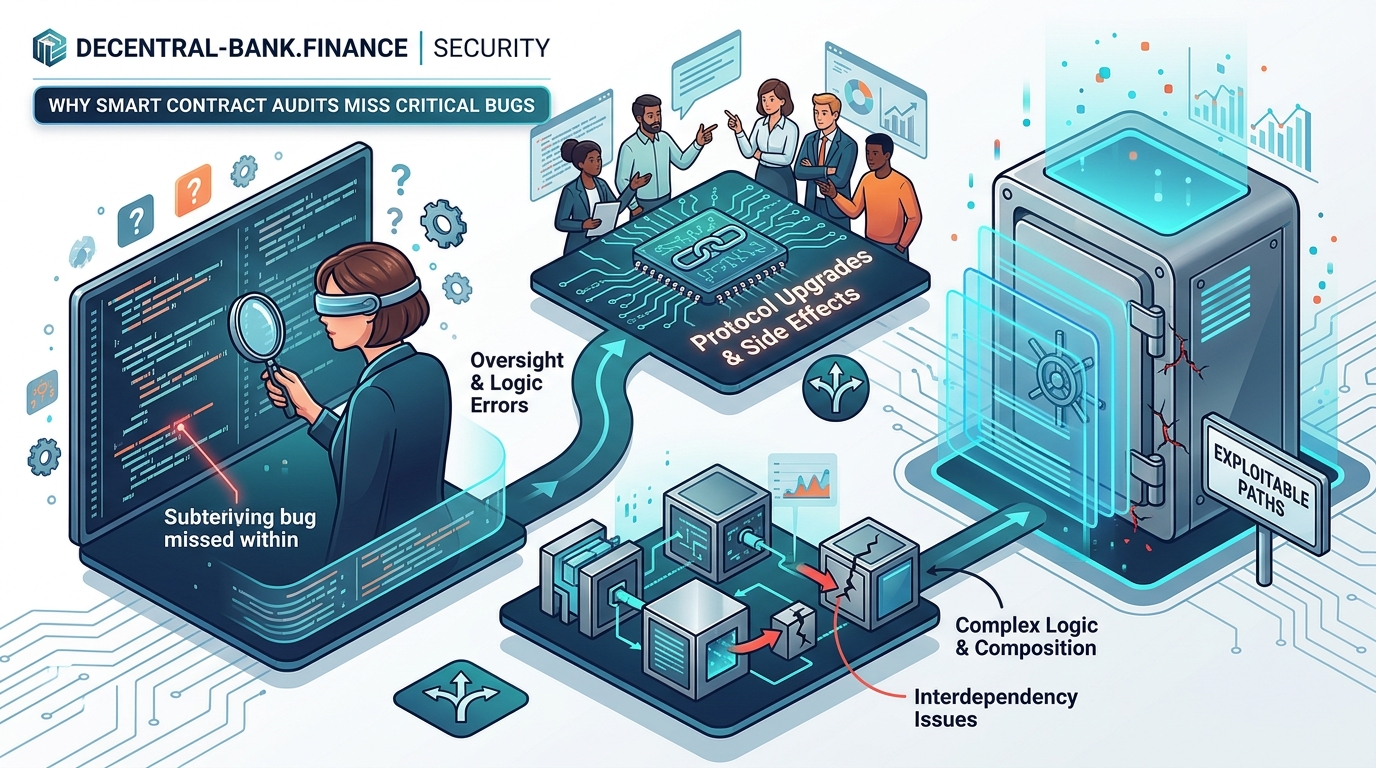
Modern protocols are incredibly complex
DeFi protocols now span multiple contracts, chains, and integrations. A single protocol might include:
- Core lending contracts
- Governance modules
- Oracle integrations
- Cross-chain bridges
- Liquidity pool interactions
- Reward distribution mechanisms
- Emergency pause functions
- Upgrade proxies
Each component introduces potential vulnerabilities. The interactions between components create emergent risks that individual contract audits miss.
Flash loan attacks exploit these complex interactions. The vulnerability exists not in one contract but in how multiple protocols interact within a single transaction.
Composability makes DeFi powerful but auditing nearly impossible. Your protocol might be secure in isolation but vulnerable when combined with others.
Economic attacks don’t show up in code reviews
Traditional audits focus on technical vulnerabilities. They check if code executes as intended. But many exploits manipulate economic mechanisms rather than exploit code bugs.
Oracle manipulation attacks work through price feed manipulation, not smart contract vulnerabilities. An attacker might:
- Take a flash loan
- Manipulate a low-liquidity pool
- Trigger liquidations in your protocol
- Profit from the price distortion
- Repay the flash loan
Your code functions perfectly throughout this attack. No reentrancy. No overflow. No access control breach. The vulnerability exists in your economic design, not your Solidity.
Liquidation mechanisms become attack vectors when protocols rely on manipulable price sources. Auditors review the liquidation code but rarely stress-test economic assumptions.
Governance token economics create similar blind spots. Your token distribution might incentivize attacks rather than prevent them. Code audits don’t catch these game theory problems.
Audit reports use careful language
Read audit reports closely. The language reveals limitations:
“No critical issues were found in the contracts within scope during the review period.”
This statement means auditors found nothing in the specific code they reviewed at that moment. It does not mean:
- The protocol is secure
- No vulnerabilities exist
- The deployed code matches reviewed code
- Integrations are safe
- Economic design is sound
Audit reports include disclaimers that most people skip. These disclaimers explicitly state that audits don’t guarantee security.
Many reports categorize findings by severity but let project teams decide which issues to fix. A “medium severity” bug might enable a critical exploit in specific conditions.
Testing environments differ from production
Auditors review code in isolated test environments. They can’t replicate mainnet conditions:
- Real user behavior patterns
- Actual liquidity levels
- Network congestion
- MEV bot activity
- Composability with live protocols
A vulnerability might only appear under specific mainnet conditions. Your protocol handles 100 test transactions perfectly but breaks at transaction 10,000 due to state bloat.
Gas optimization creates security tradeoffs. Code that works in tests might fail when gas prices spike. Users get stuck in partially executed transactions, creating exploitable states.
Smart contract approvals work differently under network stress. Race conditions emerge that test environments never expose.
The audit gap widens with protocol upgrades
Most protocols use upgradeable contracts. Teams can modify logic without redeploying. This flexibility creates security challenges.
You audit version 1.0. The report covers that specific implementation. Then you upgrade to 1.1, adding new features. The audit no longer applies to your live code.
Some teams treat minor upgrades as low risk and skip re-audits. But small changes in complex systems create unexpected interactions.
Proxy patterns introduce their own vulnerabilities. The proxy might be secure, but the upgrade mechanism could allow unauthorized changes. Auditors review the implementation but might miss proxy-specific attack vectors.
Multiple audits catch more bugs but not all bugs
Projects increasingly commission multiple audits from different firms. This improves coverage but doesn’t eliminate risk.
Different firms use different methodologies. One focuses on automated tools. Another emphasizes manual review. A third specializes in formal verification.
Each approach has blind spots. Automated tools miss business logic flaws. Manual review struggles with complex mathematical operations. Formal verification requires formal specifications that might not match actual requirements.
The table below shows how different audit approaches catch different vulnerability types:
| Audit Approach | Strengths | Blind Spots |
|---|---|---|
| Automated scanning | Fast, catches common patterns | Misses novel attacks, business logic |
| Manual code review | Finds complex logic issues | Time-intensive, human error |
| Formal verification | Proves mathematical correctness | Requires precise specs, expensive |
| Economic analysis | Catches game theory exploits | Doesn’t find code bugs |
Even with multiple audits, gaps remain. No combination covers every possible attack vector.
Auditors can’t predict future attack vectors
Security is an arms race. New attack patterns emerge constantly.
Reentrancy attacks were rare before The DAO hack in 2016. Now every auditor checks for them. But what about attack vectors that don’t exist yet?
Flash loans didn’t exist when early DeFi protocols launched. Those protocols couldn’t be audited for flash loan attacks because the concept didn’t exist.
Cross-chain bridge exploits evolved as bridges became common. Early bridge audits missed vulnerabilities that seem obvious now.
Your audit might be thorough by today’s standards but miss tomorrow’s attack patterns. Protocol security requires ongoing vigilance, not one-time reviews.
Budget constraints limit audit depth
Comprehensive audits are expensive. Tier-one firms charge $50,000 to $500,000 depending on complexity. Many projects can’t afford thorough reviews.
Budget-conscious teams might:
- Choose cheaper firms with less experience
- Reduce audit scope to save money
- Skip re-audits after code changes
- Audit only core contracts, not integrations
These compromises introduce risk. The cheapest audit might miss critical issues that experienced firms would catch.
Some projects use audit reports as marketing rather than security tools. They commission minimal reviews to claim “audited by” a known firm without investing in comprehensive security.
Formal verification fills some gaps but has limits
Formal verification mathematically proves code correctness. It catches bugs that manual review misses.
But formal verification requires:
- Writing formal specifications in mathematical notation
- Translating business requirements into provable properties
- Running verification tools that take days or weeks
- Fixing issues and re-verifying
This process is expensive and time-consuming. Few projects can afford it.
Formal verification also proves only what you specify. If your specifications don’t cover a specific edge case, verification won’t catch it. The code might be “proven correct” according to incomplete specifications.
Post-audit changes invalidate security guarantees
Teams often modify code after audits. They might:
- Fix bugs the audit identified
- Add features users requested
- Optimize gas costs
- Refactor for readability
Each change potentially introduces new vulnerabilities. The audit report explicitly states it covers only the reviewed version.
Protocol hacks often exploit post-audit modifications. Teams change a few lines without realizing the security implications.
Best practice requires re-auditing after significant changes. But tight launch deadlines pressure teams to deploy without re-review.
Anonymous teams complicate accountability
Some DeFi projects launch with anonymous teams. This makes audit coordination difficult.
Auditors can’t verify:
- Team technical competence
- Ability to fix identified issues correctly
- Commitment to ongoing security
- Response plans for discovered vulnerabilities
Anonymous protocol teams might disappear after an exploit. The audit firm has no recourse.
Reputable audit firms increasingly refuse anonymous projects or charge premium rates to compensate for added risk.
Bug bounties catch what audits miss
Continuous bug bounty programs incentivize ongoing security research. They complement audits by:
- Engaging the broader security community
- Offering rewards for finding vulnerabilities
- Creating ongoing scrutiny after launch
- Catching issues auditors missed
Major exploits have been prevented by bug bounty submissions. Researchers with fresh perspectives spot issues that original auditors overlooked.
But bug bounties have limitations. Researchers focus on high-value targets. Small protocols with modest bounties get less attention. The most critical bugs might be exploited rather than reported if bounties are too low.
Start with multiple audits from reputable firms. Add formal verification for critical components. Launch a competitive bug bounty program. Implement continuous monitoring. Security is a process, not a one-time event.
Building defense in depth
No single security measure protects completely. Effective protocol security requires layers:
- Multiple independent audits
- Formal verification of core logic
- Competitive bug bounty programs
- Gradual rollout with usage caps
- Emergency pause mechanisms
- Continuous monitoring and alerting
- Post-deployment security reviews
- Community oversight through governance tokens
Each layer catches different vulnerabilities. When one fails, others provide backup protection.
Time-locks on critical functions give users warning before dangerous changes execute. Multi-signature requirements prevent single points of failure. Circuit breakers limit damage from successful attacks.
Learning from past failures improves future security
The DeFi ecosystem learns from each exploit. Post-mortem analyses identify root causes. Security firms update their review processes. New tools emerge to catch previously unknown vulnerabilities.
Projects that suffered hacks often rebuild with significantly improved security. They understand firsthand where audits fall short.
The broader community benefits from these lessons. Attack patterns that surprised early protocols become standard checklist items for new audits.
Protocol security practices evolve continuously. What constitutes “best practice” today will seem inadequate in two years.
Why perfect security remains impossible
Smart contract security faces fundamental challenges that audits alone can’t solve.
Code complexity grows faster than security tools improve. Each new DeFi primitive introduces novel attack surfaces. Composability creates emergent risks that individual audits can’t predict.
Economic incentives drive sophisticated attacks. When protocols hold billions in TVL, attackers invest heavily in finding exploits. They have more time and motivation than auditors working under fixed budgets.
The blockchain environment constantly changes. New EVM opcodes, layer-2 solutions, and cross-chain bridges create security challenges that didn’t exist when current audit methodologies developed.
Human error remains unavoidable. Developers make mistakes. Auditors miss things. Users interact with protocols in unexpected ways.
Moving forward with realistic expectations
Understanding why audits fail helps you make better security decisions.
Don’t treat audit reports as security guarantees. View them as one data point in ongoing risk assessment.
Commission multiple audits from firms with different specializations. Combine automated scanning, manual review, and formal verification.
Launch gradually with conservative parameters. Implement usage caps and emergency controls. Monitor continuously for suspicious activity.
Build relationships with security researchers. Offer competitive bug bounties. Respond quickly to reported vulnerabilities.
Accept that perfect security is impossible. Focus on reducing risk to acceptable levels and having response plans ready.
The goal is not eliminating all vulnerabilities but building protocols resilient enough to survive the inevitable security challenges. Audits are essential but insufficient. They’re the beginning of security work, not the end.





