Crypto rug pulls drain billions from investors every year. These scams happen when project teams vanish with investor funds, leaving holders with worthless tokens. The good news? Most rug pulls follow predictable patterns, and you can learn to spot them before risking your money.
Avoiding crypto rug pulls requires checking liquidity locks, verifying team identities, analyzing token contracts, and using free security tools. Most scams reveal warning signs through unlimited token minting, anonymous teams, unrealistic promises, and suspicious tokenomics. Smart investors verify projects through multiple security checks before committing funds, protecting themselves from the most common crypto scams.
Understanding what makes a rug pull possible
Rug pulls succeed because of how decentralized finance works. Anyone can create a token and launch a liquidity pool in minutes.
No gatekeepers exist in how does DeFi actually work without banks or middlemen. This freedom creates innovation but also enables fraud.
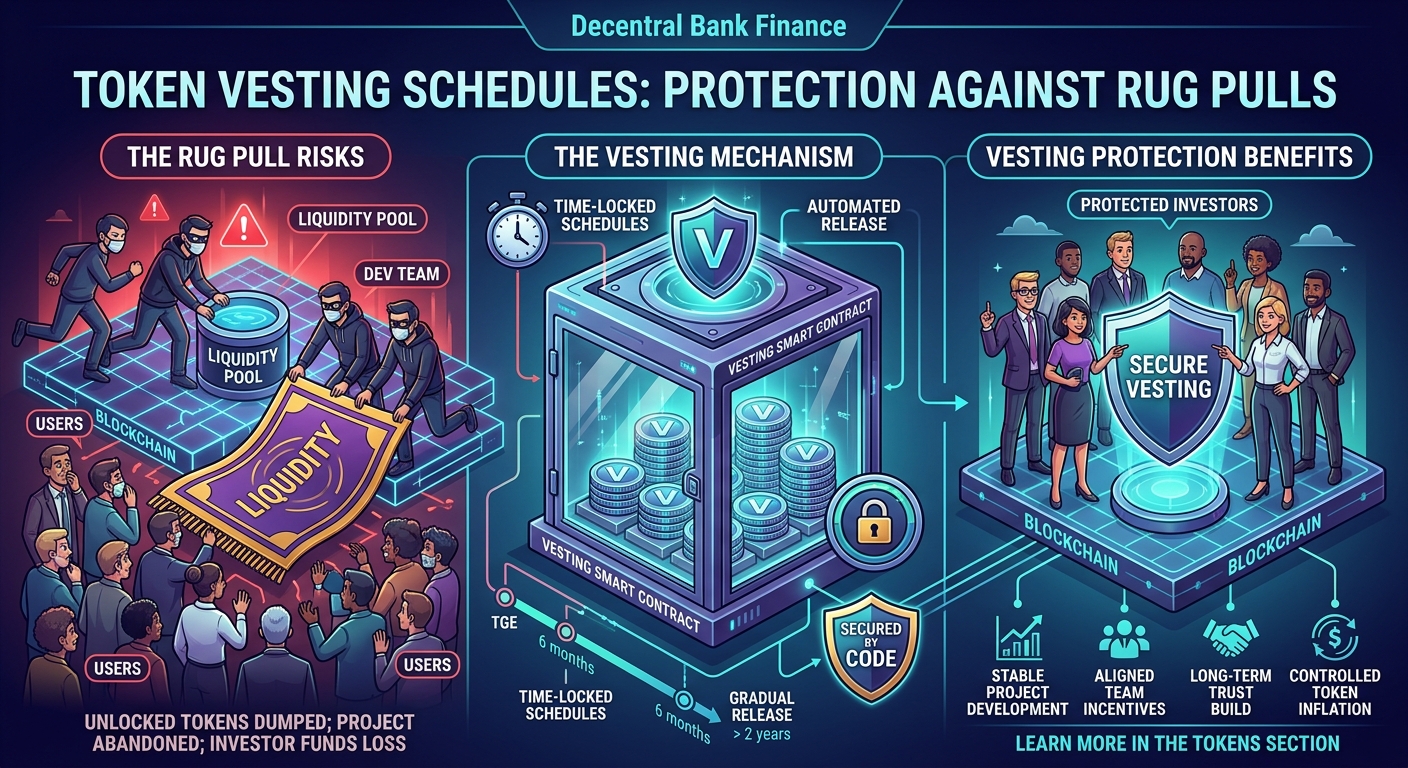
Three main types of rug pulls exist:
- Liquidity stealing: Developers remove all liquidity from the pool, making tokens unsellable
- Limiting sell orders: Code prevents anyone except creators from selling
- Dumping: Teams sell massive token holdings, crashing the price to zero
Each type leaves different traces you can detect before investing.
Red flags that scream danger
Certain warning signs appear in nearly every rug pull. Learning to recognize them saves your money.
Anonymous teams top the list. Legitimate projects have public founders with verified identities and track records. Scammers hide behind cartoon avatars and fake names.
Missing or unverified smart contract code ranks second. Reputable projects publish their code and get audits. Scammers keep contracts hidden or use unverified code.
Unrealistic return promises follow closely. If a project guarantees 1,000% APY with zero risk, run away. Why DeFi yields are high and what risks you’re actually taking explains why sustainable returns require accepting real risks.
Pressure tactics create urgency. “Limited time only” or “Get in before it’s too late” messaging pushes emotional decisions instead of rational analysis.
Checking liquidity locks before investing
Liquidity locks prevent developers from draining pools. They prove teams commit to long-term success rather than fast exits.
Here’s how to verify liquidity locks:
- Find the project’s liquidity pool on the DEX (Uniswap, PancakeSwap, etc.)
- Check the pool’s liquidity provider (LP) tokens
- Verify LP tokens are locked using services like Unicrypt or Team Finance
- Confirm lock duration extends at least six months, preferably longer
Unlocked liquidity means developers can remove all funds instantly. Never invest without verified locks.
Some scammers create fake lock certificates. Always verify locks through the actual locking service, not screenshots or PDFs shared by the team.
Analyzing token contracts for hidden dangers
Smart contract code reveals a project’s true intentions. Malicious functions hide in plain sight for those who know where to look.
Key contract features to check:
| Feature | Safe | Dangerous |
|---|---|---|
| Minting function | Disabled or capped | Unlimited minting enabled |
| Ownership | Renounced or time-locked | Single owner with full control |
| Transfer restrictions | Equal for all holders | Owner can block sells |
| Fee structure | Reasonable (under 10% total) | Excessive (over 15%) or changeable |
| Blacklist function | Absent | Present and owner-controlled |
Tools like BSCCheck, Token Sniffer, and Honeypot.is analyze contracts automatically. They flag dangerous functions in seconds.
What happens when you approve a smart contract explains why understanding contract permissions protects your funds beyond just the initial investment.
Verifying team identity and background
Real teams use real names and show real faces. They maintain active social media with genuine engagement.
Check these identity markers:
- LinkedIn profiles with work history and connections
- GitHub accounts with code contributions
- Previous successful projects with verifiable outcomes
- Video appearances at conferences or AMAs
- Doxxing verification through third-party services
Should you trust a DeFi protocol with an anonymous team covers when anonymity makes sense and when it signals danger.
Research team members individually. Search their names with “scam” or “rug pull” added. Check crypto community forums for mentions.
Fake LinkedIn profiles exist but lack depth. Real profiles show years of activity, recommendations, and connections to other verified people.
Using free security tools effectively
Multiple free platforms scan projects for rug pull indicators. Using several tools together provides comprehensive protection.
Essential security tools:
- Token Sniffer: Scans contracts for malicious code patterns
- RugDoc: Reviews projects and rates their safety
- DexTools: Shows holder distribution and liquidity metrics
- Etherscan/BscScan: Verifies contract code and transactions
- CertiK Skynet: Provides automated security scores
5 free tools to check if a DeFi protocol is safe offers detailed guides for each platform.
Run every project through at least three different tools. One tool might miss what another catches.
Pay attention to holder distribution. If the top ten wallets control over 50% of supply, price manipulation becomes trivial.
Recognizing suspicious tokenomics
Token economics reveal whether a project can sustain value or inevitably collapses.
Warning signs in tokenomics:
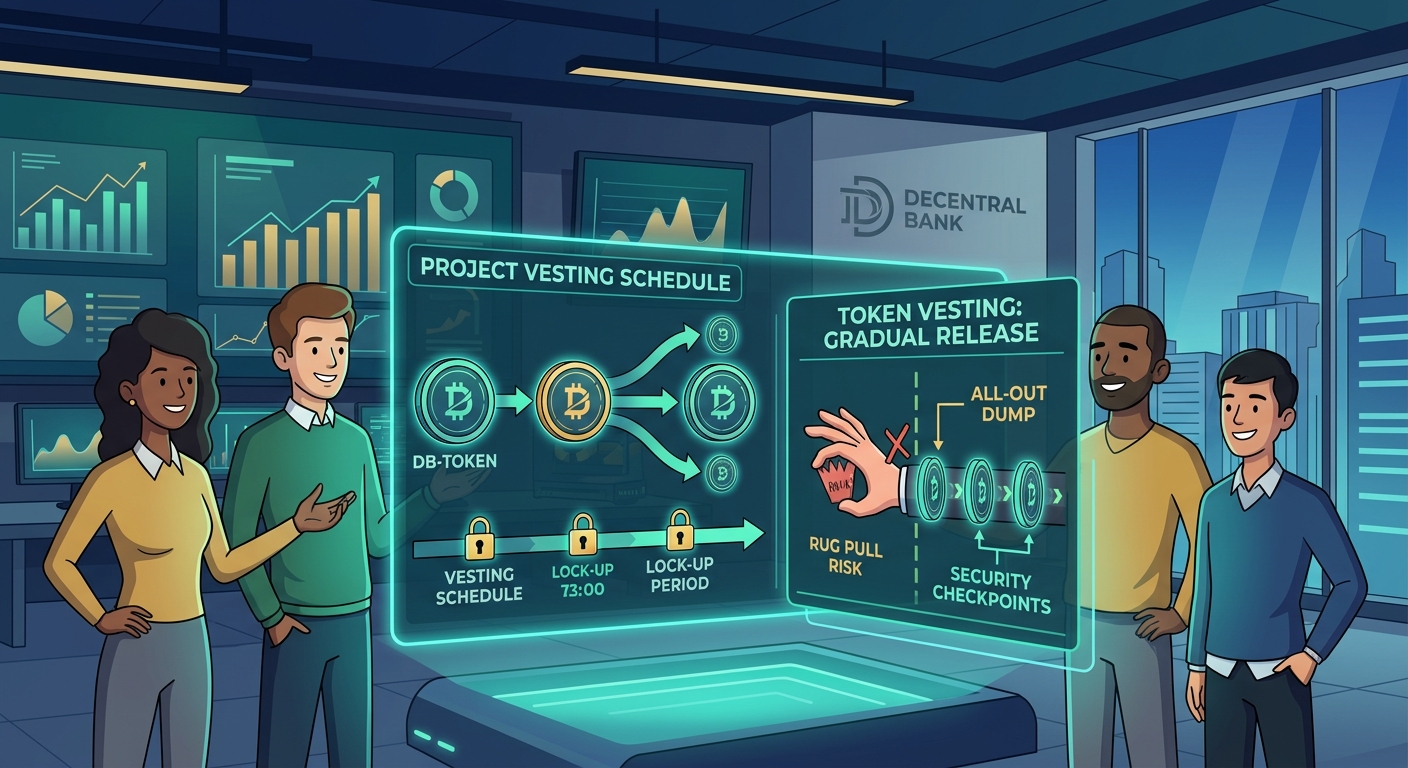
- Team allocations exceeding 20% of total supply
- No vesting schedules for team tokens
- Excessive transaction taxes (over 10% combined)
- Reflection mechanisms that mainly benefit large holders
- Burn mechanisms controlled by the team
Smart tokenomics align team incentives with holder success. When teams can dump massive allocations immediately, they will. Vesting schedules prove commitment to long-term value creation rather than short-term extraction.
How token distribution models impact your long-term investment returns breaks down how different allocation strategies affect your investment.
Calculate potential dilution. If 30% of tokens remain unvested, your holdings lose 30% of relative value when those tokens enter circulation.
Checking community engagement quality
Fake engagement floods rug pull projects. Real communities show organic growth and genuine discussions.
Signs of fake communities:
- Telegram groups where only admins can post
- Twitter followers with no profile pictures or posts
- Reddit accounts created recently with identical comment patterns
- Discord servers with thousands of members but no conversation
- Comments praising the project without substance
Real communities debate. Members ask tough questions about tokenomics, security, and roadmap feasibility. Teams answer directly rather than deleting critical posts.
Check when social media accounts were created. Legitimate projects build communities over months. Scams spin up accounts days before launch.
Look at engagement rates. A Twitter account with 50,000 followers but 10 likes per post bought followers.
Auditing audit reports properly
Security audits provide legitimacy, but not all audits are created equal. Some audit firms rubber-stamp anything for payment.
Reputable audit firms include:
- CertiK
- PeckShield
- Trail of Bits
- ConsenSys Diligence
- OpenZeppelin
Lesser-known firms might provide thorough audits or meaningless stamps. Research the auditor before trusting their report.
Read the actual audit report. Don’t just accept “audited by X” claims. Check for:
- Critical and high-severity issues found
- Whether identified issues were fixed
- When the audit occurred (recent audits matter more)
- Whether the deployed contract matches the audited version
Is your DeFi investment safe? Understanding smart contract audits explains what audits can and cannot guarantee.
Some teams get audits, then change the code afterward. Verify the deployed contract matches the audited version by comparing contract addresses and deployment timestamps.
Watching for pump and dump patterns
Rug pulls often follow specific price patterns before the final exit. Recognizing these patterns helps you exit before losses mount.
Common pump and dump signals:
- Coordinated buying that spikes price 300% in hours
- Heavy marketing push right before price peaks
- Team members or influencers suddenly going quiet
- Large wallets moving tokens to exchanges
- Liquidity starting to decrease gradually
Price charts reveal manipulation. Natural growth shows steady upward trends with normal corrections. Manipulation shows vertical spikes followed by plateaus before crashes.
Monitor the team’s activity level. When developers stop responding to questions or delay promised updates, they might be preparing to exit.
Check transaction history for the team wallet. If they’re moving tokens to exchanges or new wallets, an exit could be imminent.
Creating your personal security checklist
Systematic checking prevents emotional decisions. Use the same process for every project.
Your pre-investment checklist:
- Verify team identity through multiple sources
- Confirm liquidity locks for at least six months
- Scan contract code with three different tools
- Read the full audit report if one exists
- Calculate token distribution and vesting schedules
- Check holder concentration in top wallets
- Verify community engagement authenticity
- Research team’s previous projects
- Confirm social media accounts have real history
- Wait 24 hours before investing to avoid FOMO
Never skip steps because a project seems legitimate. Scammers specifically design projects to appear trustworthy.
How to spot a rug pull before you lose your crypto provides additional specific indicators to watch for.
Document your research. Writing down findings forces thorough analysis and creates records for future reference.
Learning from past rug pulls
Studying previous scams teaches pattern recognition. The same tactics repeat across different projects.
Notable rug pulls and their lessons:
- Squid Game Token: Anonymous team, no sell function for regular holders, disappeared with $3.3 million
- Meerkat Finance: Audited project, developers still drained $31 million hours after launch
- AnubisDAO: Raised $60 million, developer vanished same day, never deployed actual protocol
Each case shows that single security measures aren’t enough. Squid had marketing hype. Meerkat had an audit. AnubisDAO had a popular concept.
Only comprehensive security checks catch scams reliably.
How to protect yourself from DeFi rug pulls and exit scams analyzes multiple case studies with specific lessons from each.
Protecting yourself beyond initial research
Ongoing monitoring matters as much as initial due diligence. Projects can become rug pulls after launching legitimately.
Post-investment protection strategies:
- Set price alerts for significant drops
- Monitor team wallet activity weekly
- Check liquidity levels regularly
- Watch for sudden changes in transaction taxes
- Track whether roadmap milestones get met
- Stay active in community channels for warning signs
Taking profits periodically reduces risk. Never let a single position grow beyond what you can afford to lose completely.
Consider understanding collateral ratios: the key to safe DeFi borrowing principles when managing position sizes.
Use stop-losses where possible. Some DEXs support limit orders that automatically sell if prices drop below certain thresholds.
Building knowledge through education
Understanding 7 common DeFi terms every beginner should know before getting started strengthens your ability to evaluate projects critically.
The more you understand about how protocols work, the easier spotting scams becomes. Education creates intuition that flags problems before detailed analysis.
Join educational communities focused on security. Members share new scam tactics and warning signs as they emerge.
Practice analyzing established, legitimate projects first. Learn what good tokenomics, transparent teams, and solid code look like before evaluating newer projects.
Taking action with confidence
Avoiding rug pulls doesn’t require paranoia or avoiding DeFi entirely. It requires systematic verification and disciplined decision-making.
Start with established projects that have operated successfully for years. Build experience and knowledge before exploring newer opportunities.
Your security checklist becomes faster with practice. What takes an hour initially becomes a 15-minute process as you develop efficiency.
Remember that missing opportunities costs less than losing capital to scams. Better to skip ten legitimate projects than to invest in one rug pull.
Stay patient, stay systematic, and your crypto investments will remain safer than most participants in the space.





