You’ve heard about the incredible opportunities in decentralized finance. Maybe you’re ready to earn yield on your crypto or try your first token swap. But here’s the reality: DeFi’s openness comes with serious security risks that can drain your wallet in seconds if you’re not careful. One wrong click on a malicious smart contract, one compromised seed phrase, or one overlooked approval can cost you everything.
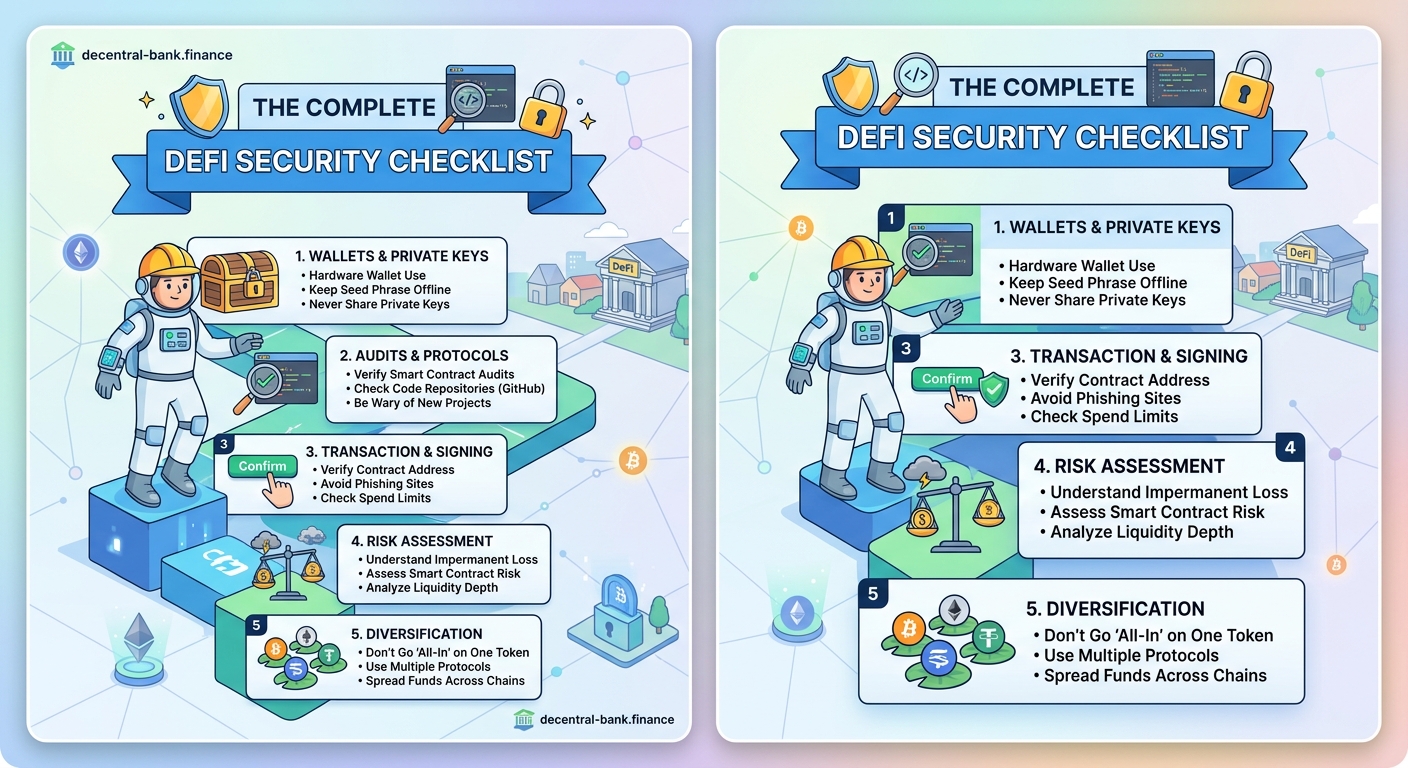
This DeFi security checklist covers wallet protection, smart contract safety, transaction verification, and scam prevention. By following these practical steps, you’ll protect your digital assets from the most common threats in decentralized finance. Security isn’t optional in DeFi, it’s the foundation of safe participation. Master these fundamentals before risking real money.
Understanding why DeFi security is different
Traditional banks protect your money with insurance, fraud departments, and customer service teams. DeFi works the opposite way.
You are the bank. You are the security team. You are the customer service department.
There’s no phone number to call if someone drains your wallet. No fraud protection department to reverse unauthorized transactions. No insurance policy covering smart contract bugs.
This isn’t meant to scare you away. It’s meant to prepare you. Understanding how does DeFi actually work without banks or middlemen helps you see why security responsibility falls entirely on your shoulders.
The good news? Most DeFi losses are preventable. They happen because people skip basic security steps, not because the technology itself is fundamentally broken.
Securing your wallet before anything else

Your wallet is your entire DeFi identity. Lose access to it, and you lose everything inside. Let someone else access it, and they can drain it completely.
Choose the right wallet type for your needs
Hot wallets stay connected to the internet. They’re convenient for frequent transactions but more vulnerable to attacks.
Cold wallets stay offline. They’re safer for long-term storage but less convenient for active DeFi participation.
Most beginners should start with a reputable hot wallet for small amounts while learning. Once you’re comfortable and holding significant value, move most funds to cold storage.
The guide on how to choose between hot wallets and cold wallets for your crypto breaks down exactly when each type makes sense.
Protect your seed phrase like your life depends on it
Your seed phrase is typically 12 or 24 words that give complete access to your wallet. Anyone who has these words controls your funds forever.
Never store your seed phrase digitally. No photos. No cloud storage. No password managers. No email drafts.
Write it on paper or metal. Store copies in multiple secure physical locations. Never let anyone see it, photograph it, or “verify” it for any reason.
If you’re wondering what happens if you lose your seed phrase, the short answer is: your funds are gone forever. There’s no recovery process. No customer support can help you.
Avoid these critical wallet setup mistakes
Common mistakes can compromise your wallet before you even start using it:
- Using a wallet you didn’t download directly from the official source
- Setting up your wallet on a compromised or infected device
- Taking a screenshot of your seed phrase
- Storing your seed phrase in the same location as your device
- Reusing the same password across multiple services
- Skipping two-factor authentication when available
The article on 5 critical mistakes beginners make when setting up their first DeFi wallet covers these traps in detail with real examples.
Verifying protocols before connecting your wallet
Not all DeFi protocols are legitimate. Some are outright scams. Others are well-intentioned but poorly secured.
Check these indicators before using any protocol
- Look for a professional, detailed website with clear documentation
- Verify the team is public and has a track record in crypto
- Confirm the smart contracts have been audited by reputable firms
- Check the protocol’s total value locked (TVL) and user count
- Read recent community discussions on Twitter and Discord
- Search for any past security incidents or exploits
- Verify the protocol has been running for at least several months
A protocol missing most of these indicators might still be legitimate, but it’s definitely higher risk.
Use these free security tools
Several platforms help you evaluate protocol safety:
| Tool | What It Checks | Best For |
|---|---|---|
| DeFi Safety | Audit quality and process quality scores | Overall protocol assessment |
| Token Sniffer | Token contract code for common scams | New token evaluation |
| Etherscan | Contract verification and transaction history | Ethereum-based protocols |
| CertiK Skynet | Real-time security monitoring | Active threat detection |
The resource on 5 free tools to check if a DeFi protocol is safe shows you exactly how to use each one.
Understand what smart contract audits actually mean
An audit doesn’t guarantee safety. It means professional security researchers reviewed the code and documented what they found.
Audited protocols still get hacked. Auditors miss bugs. Code gets updated after audits. New attack vectors emerge.
But audits significantly reduce risk. A protocol with multiple audits from respected firms is generally safer than one with no audits at all.
Learn more about why smart contract audits still miss critical bugs to set realistic expectations.
Managing smart contract approvals safely
Every time you use a DeFi protocol, you typically need to approve it to access your tokens. These approvals create ongoing security risks many beginners don’t understand.
What happens when you approve a smart contract
When you approve a contract, you’re giving it permission to move specific tokens from your wallet. Most protocols request unlimited approval by default.
This means the protocol can access those tokens anytime, even months or years later. If the protocol gets hacked or turns malicious, your approved tokens are at risk.
The explainer on what happens when you approve a smart contract walks through the technical details in plain language.
Limit your approval amounts
Instead of approving unlimited access, approve only what you need for your immediate transaction.
Most wallet interfaces hide this option, but it’s usually available in advanced settings. Approving exactly the amount you’re about to use adds an extra step but dramatically reduces risk.
Regularly revoke old approvals
Your wallet likely has dozens of active approvals you’ve forgotten about. Each one is a potential vulnerability.
Use tools like Revoke.cash or Etherscan’s token approval checker to see all your active approvals. Revoke any you’re not actively using.
Make this a monthly habit, like checking your bank statements.
Recognizing and avoiding common DeFi scams
Scammers constantly develop new tactics, but most DeFi scams follow predictable patterns.
Red flags that signal a likely scam
- Guaranteed high returns with no risk mentioned
- Pressure to invest immediately before an “opportunity” closes
- Anonymous team with no verifiable credentials
- Brand new protocol with massive promised yields
- Token contracts that can’t be sold after buying
- Requests to send crypto to “verify” your wallet
- Direct messages offering investment advice or support
- Websites with spelling errors or unprofessional design
If something seems too good to be true in DeFi, it almost certainly is.
How rug pulls actually work
A rug pull happens when developers drain liquidity from a protocol, making it impossible for users to sell their tokens.
Common rug pull tactics include:
- Minting massive amounts of new tokens and dumping them
- Removing all liquidity from decentralized exchanges
- Implementing hidden code that blocks selling
- Abandoning the project after initial fundraising
The guide on how to spot a rug pull before you lose your crypto teaches you to identify these schemes early.
“The best defense against DeFi scams isn’t technical knowledge, it’s skepticism. Question everything, especially opportunities that promise exceptional returns. Legitimate protocols focus on building sustainable systems, not making you rich overnight.”
Protecting yourself during transactions
Even when using legitimate protocols, individual transactions carry risks.
Double-check every transaction detail
Before confirming any transaction, verify:
- The receiving address is correct (check first and last characters)
- The token amount matches what you intended
- The gas fee is reasonable for current network conditions
- You’re interacting with the correct smart contract
- The transaction type matches your intended action
One wrong character in an address means your funds go to the wrong wallet forever. There’s no undo button.
Understand slippage settings
Slippage is the difference between the expected price and the actual execution price of your trade.
Setting slippage too low means your transaction will fail. Setting it too high means you might get a terrible price.
For most trades on established protocols, 0.5% to 1% slippage is reasonable. Higher slippage is sometimes necessary for smaller liquidity pools but increases your risk of front-running attacks.
The article on what is slippage and why does it eat your profits explains how to optimize this setting.
Test with small amounts first
Never risk significant funds on your first transaction with a new protocol.
Send a small test amount first. Verify it works as expected. Only then proceed with larger amounts.
This simple habit has saved countless users from catastrophic losses.
Building safe DeFi habits for the long term
Security isn’t a one-time checklist. It’s an ongoing practice.
Create a security routine
Establish regular security practices:
- Weekly: Review recent transactions for anything unexpected
- Monthly: Check and revoke unnecessary token approvals
- Quarterly: Update wallet software and review security settings
- Annually: Verify your seed phrase backup is still accessible and secure
Stay informed about current threats
The DeFi security landscape changes constantly. New attack vectors emerge. Protocols get exploited. Scam tactics evolve.
Follow reputable security researchers on Twitter. Join community forums. Read post-mortem reports when protocols get hacked.
Learning from others’ mistakes is much cheaper than making them yourself.
Use separate wallets for different purposes
Consider maintaining multiple wallets:
- A “hot” wallet with small amounts for frequent transactions
- A “warm” wallet for medium-term holdings and active DeFi positions
- A “cold” wallet for long-term storage that rarely connects to anything
This compartmentalization limits damage if one wallet gets compromised.
The comparison of browser extension vs mobile wallet apps helps you choose the right setup.
Know when hardware wallets make sense
Hardware wallets provide the highest security for most users. They keep your private keys on a physical device that never connects directly to the internet.
But they cost money and add friction to frequent transactions. They’re not necessary when you’re starting with small amounts, but become increasingly important as your holdings grow.
The analysis of should you use a hardware wallet helps you decide when to make this investment.
Understanding the risks you can’t eliminate
Even perfect security practices can’t protect you from every DeFi risk.
Smart contract bugs affect everyone
No amount of personal security stops a protocol-level exploit. If the smart contract itself has a vulnerability, all users are at risk regardless of their individual practices.
This is why protocol selection matters so much. Choosing established, audited protocols with proven track records significantly reduces this risk.
Network-level attacks happen
Blockchain networks themselves occasionally face attacks or technical failures. Reorganizations, consensus failures, and validator issues can affect your transactions.
These events are rare on major networks like Ethereum, but they’re not impossible.
Regulatory changes create uncertainty
Governments worldwide are still figuring out how to regulate DeFi. Future regulatory actions could affect protocol availability, token values, or your ability to access certain services.
This isn’t a security risk in the traditional sense, but it’s a risk to be aware of.
Responding if something goes wrong
Despite your best efforts, you might still encounter security issues.
Signs your wallet might be compromised
Watch for these warning signs:
- Transactions you didn’t authorize appearing in your history
- Token balances decreasing without your action
- New token approvals you didn’t grant
- Wallet asking you to sign suspicious transactions
If you see any of these, assume your wallet is compromised and act immediately.
The guide on 7 warning signs your crypto wallet has been compromised provides detailed response steps.
Immediate actions if you’re compromised
- Stop using the compromised wallet immediately
- Create a new wallet on a clean device
- Transfer any remaining funds to the new wallet
- Revoke all token approvals from the compromised wallet
- Document everything for potential future reference
- Report the incident to relevant platforms and communities
Speed matters. Attackers often drain compromised wallets within minutes.
Learning from security incidents
When protocols get hacked or users lose funds, read the post-mortem analyses. Understand what went wrong. Apply those lessons to your own security practices.
The crypto community is remarkably transparent about security failures. Take advantage of this collective learning.
Your security foundation starts now
DeFi security might seem overwhelming at first. There’s a lot to remember. Many potential threats. Constant vigilance required.
But here’s the truth: most users who follow basic security practices never experience significant losses. The fundamentals covered in this checklist protect you from 95% of common threats.
Start with the basics. Secure your wallet properly. Verify protocols before using them. Check every transaction carefully. Build these habits gradually until they become automatic.
You don’t need to be a security expert to participate safely in DeFi. You just need to be consistently careful and willing to learn from the community’s collective experience.
Your financial sovereignty in DeFi is worth protecting. Take these security steps seriously from day one, and you’ll build a foundation that keeps your assets safe as you grow your DeFi knowledge and participation.





