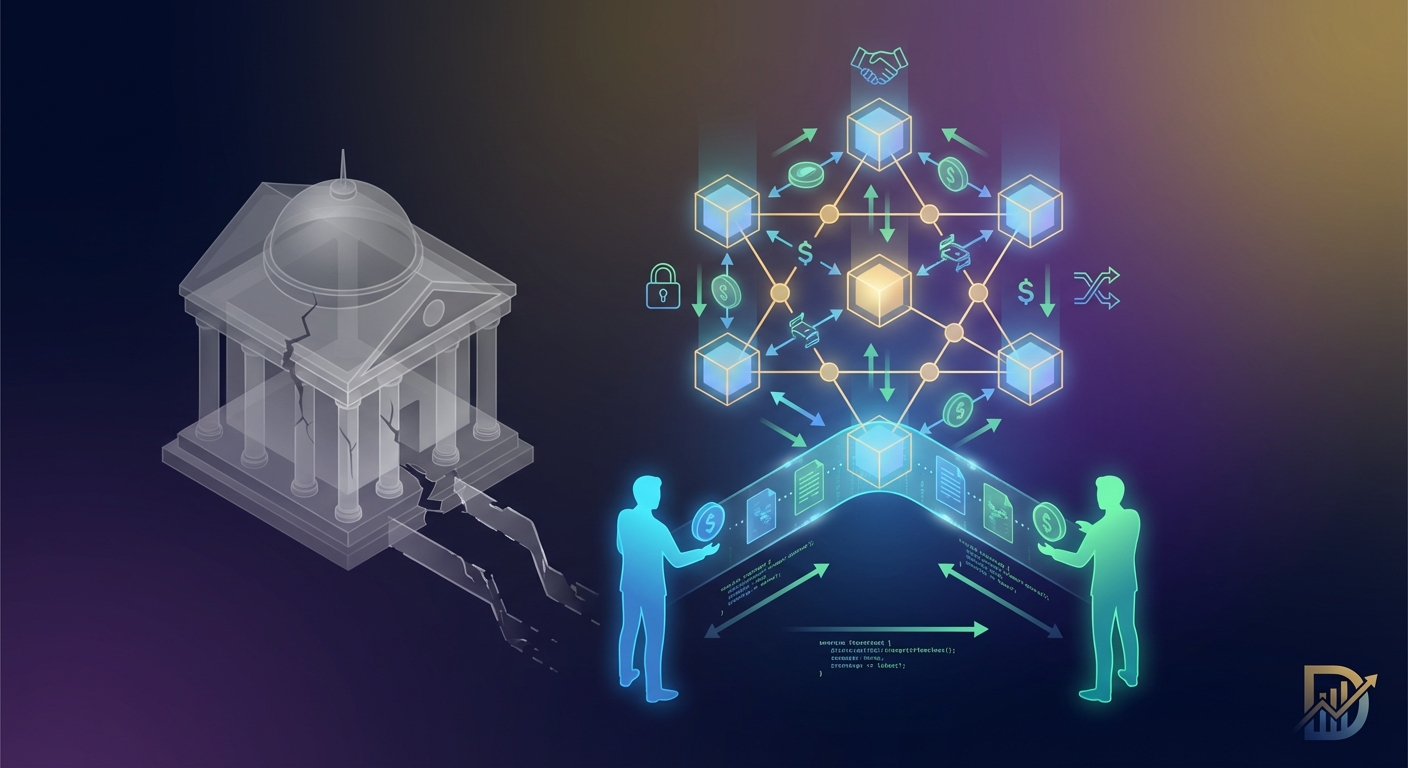
The regulatory landscape for decentralized finance shifted dramatically in 2024. What started as informal guidance from financial authorities has transformed into concrete frameworks that DeFi protocols must now address. For the first time, major platforms are implementing compliance measures that were unthinkable just two years ago.
DeFi regulations 2024 have prompted major protocols to adopt KYC systems, geographic restrictions, and enhanced transparency measures. While some platforms maintain decentralization through governance tokens and offshore structures, others are partnering directly with regulators. Users now face trade-offs between compliance-focused platforms offering legal clarity and permission-less alternatives with greater privacy but higher regulatory risk.
The regulatory frameworks reshaping DeFi
Three major regulatory developments defined 2024 for decentralized finance platforms.
The European Union’s Markets in Crypto-Assets Regulation (MiCA) took full effect in January 2024. This framework requires DeFi platforms serving EU citizens to register with national authorities, implement customer identification procedures, and maintain operational transparency. The rules apply even to protocols without traditional corporate structures.
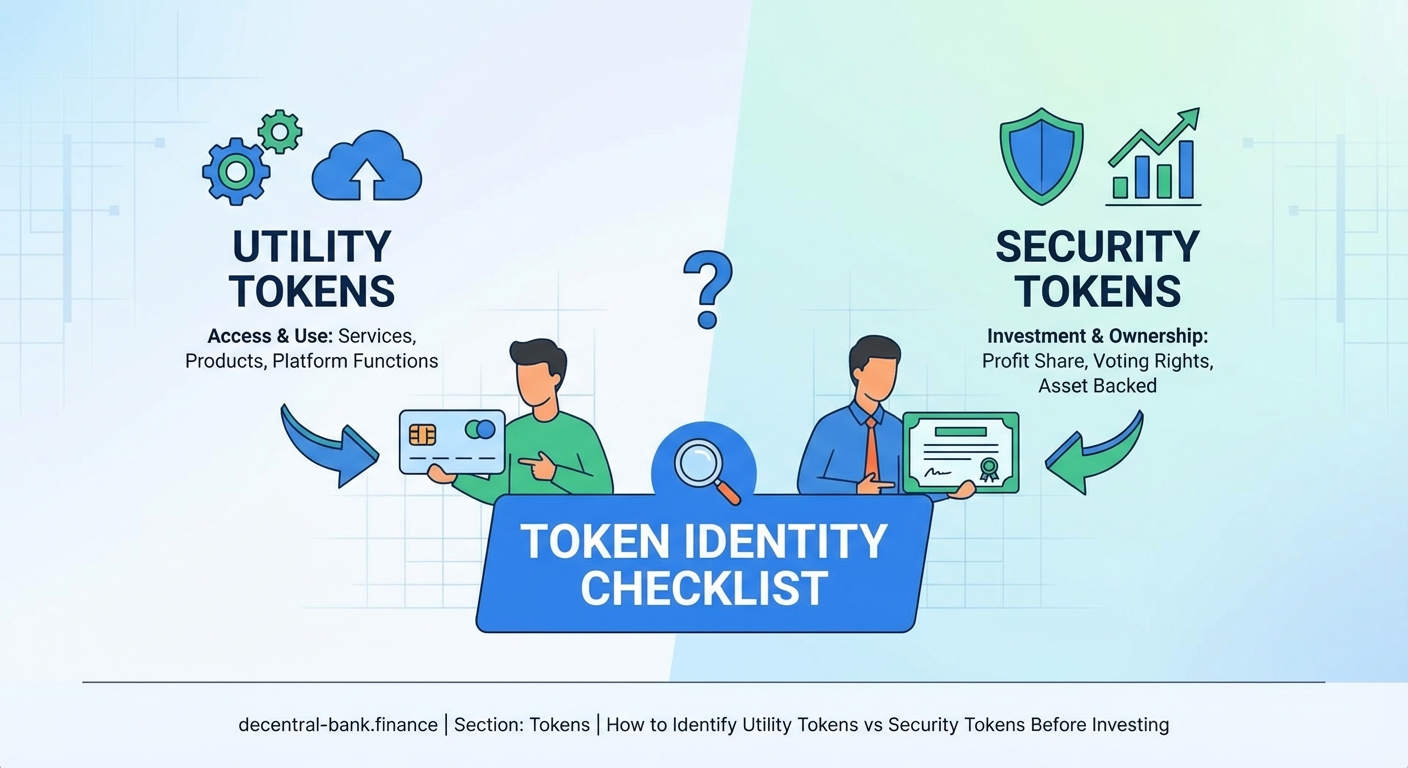
In the United States, the Securities and Exchange Commission published its DeFi enforcement framework in March 2024. The guidance clarifies when governance tokens constitute securities and establishes criteria for determining which protocols fall under securities law. The framework focuses on control, profit expectations, and the role of development teams.
Asia saw coordinated action from Singapore, Hong Kong, and Japan. These jurisdictions released aligned licensing requirements for DeFi platforms, creating a regional standard that simplifies compliance for protocols operating across multiple Asian markets.
How major protocols are responding
Different platforms have chosen different paths to address these new requirements.
Uniswap introduced a compliance layer in February 2024. Users accessing the protocol through the official interface now complete identity verification for transactions exceeding $10,000. The smart contracts themselves remain permission-less, but the primary user interface implements geographic restrictions blocking access from sanctioned jurisdictions.
Aave took a governance-first approach. The protocol’s token holders voted to establish a legal entity in Switzerland that serves as the official operator for regulatory purposes. This entity handles compliance obligations while the protocol maintains its decentralized governance structure. Users in regulated jurisdictions interact through compliant interfaces, while the core protocol remains accessible through alternative frontends.
Compound Finance split into two versions. Compound v3 continues operating without restrictions, while Compound Pro launched as a fully compliant version with KYC requirements, transaction monitoring, and regulatory reporting. Users choose which version aligns with their needs and risk tolerance.
MakerDAO restructured its entire governance framework. The protocol established SubDAOs with specific geographic focuses, each registered in different jurisdictions. This structure allows the protocol to meet varied regulatory requirements while maintaining decentralized decision-making for core protocol functions.
“The biggest challenge isn’t implementing compliance technology. It’s maintaining the core values of decentralization while meeting legitimate regulatory concerns about financial crime and consumer protection.” – Regulatory compliance specialist at a top-five DeFi protocol
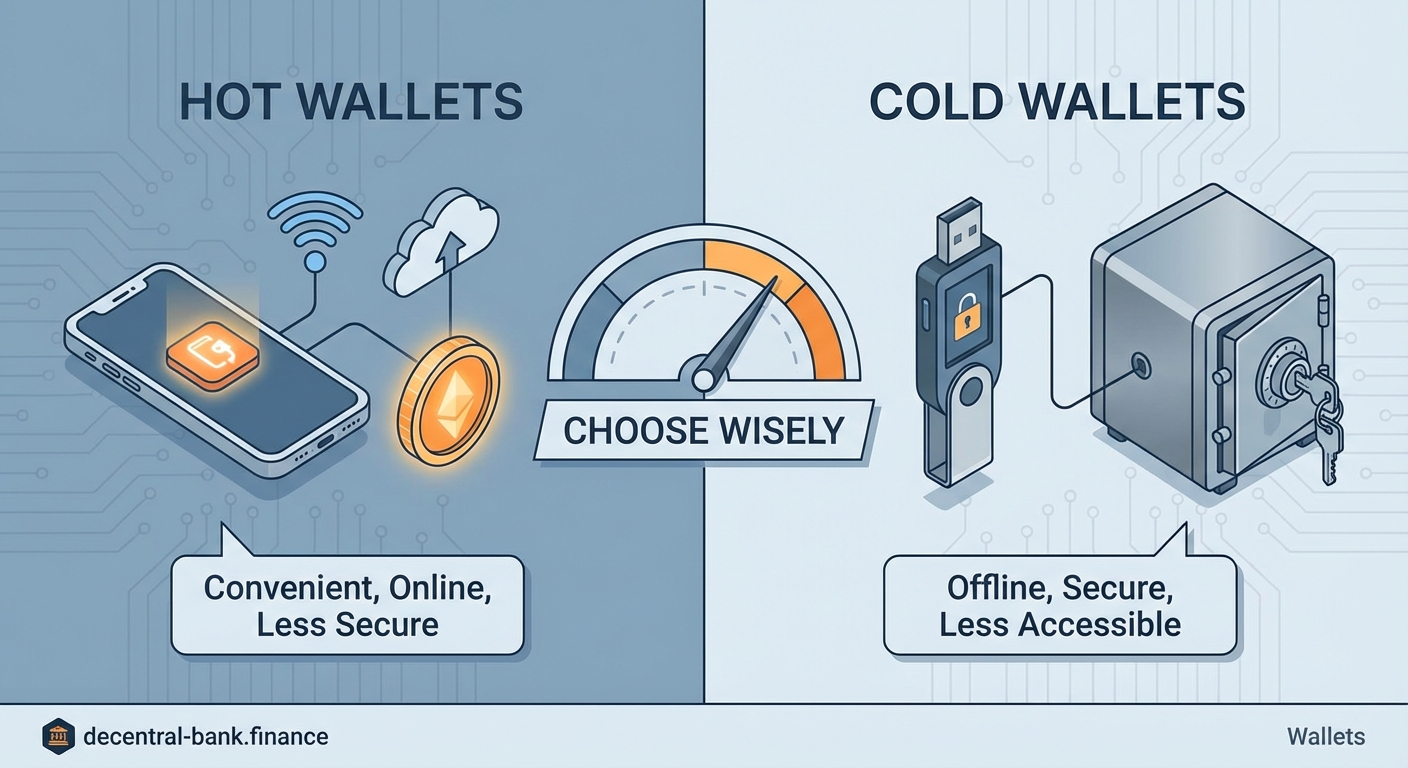
Compliance technologies entering the DeFi space
New technical solutions have emerged to help protocols meet regulatory requirements without sacrificing decentralization.
Zero-knowledge proof systems now enable identity verification without exposing personal data on-chain. Users prove they meet compliance requirements (age, jurisdiction, non-sanctioned status) without revealing their actual identity. Several protocols adopted these systems in mid-2024.
Decentralized identifier (DID) frameworks gained traction. These systems let users maintain a single verified identity across multiple protocols, reducing friction while meeting Know Your Customer requirements. The user controls their data and chooses which platforms can access it.
On-chain analytics tools became more sophisticated. Protocols now use transaction pattern analysis to identify potentially suspicious activity without collecting personal information upfront. This risk-based approach focuses compliance resources on high-risk transactions.
The KYC debate within DeFi communities
Identity verification requirements sparked intense debate among protocol communities.
Arguments supporting KYC implementation include:
- Reduced regulatory enforcement risk protects protocol developers and token holders
- Institutional adoption requires compliance with existing financial regulations
- Consumer protection measures prevent fraud and scams
- Access to traditional banking services becomes possible with proper licensing
Arguments against mandatory KYC include:
- Privacy erosion contradicts core cryptocurrency principles
- Centralized identity databases create honeypots for hackers
- Financial exclusion affects users in authoritarian regimes or without government IDs
- Competitive disadvantage compared to fully decentralized alternatives
Many protocols found middle ground through optional compliance tiers or separate compliant versions.
Geographic restrictions and VPN usage
Location-based access controls became standard across major DeFi platforms in 2024.
Most protocols now block IP addresses from sanctioned countries and jurisdictions with unclear regulatory status. These restrictions apply at the interface level, not the smart contract level. Technically sophisticated users can still access protocols through alternative means.
VPN usage to bypass geographic restrictions creates legal gray areas. Users accessing restricted services through VPNs may violate terms of service and potentially face legal consequences in their home jurisdictions. Some protocols actively detect and block known VPN IP addresses.
The situation creates a two-tier system. Users in compliant jurisdictions access feature-rich, legally clear platforms. Users elsewhere face restricted access, higher risks, or must use fully decentralized alternatives with less user-friendly interfaces.
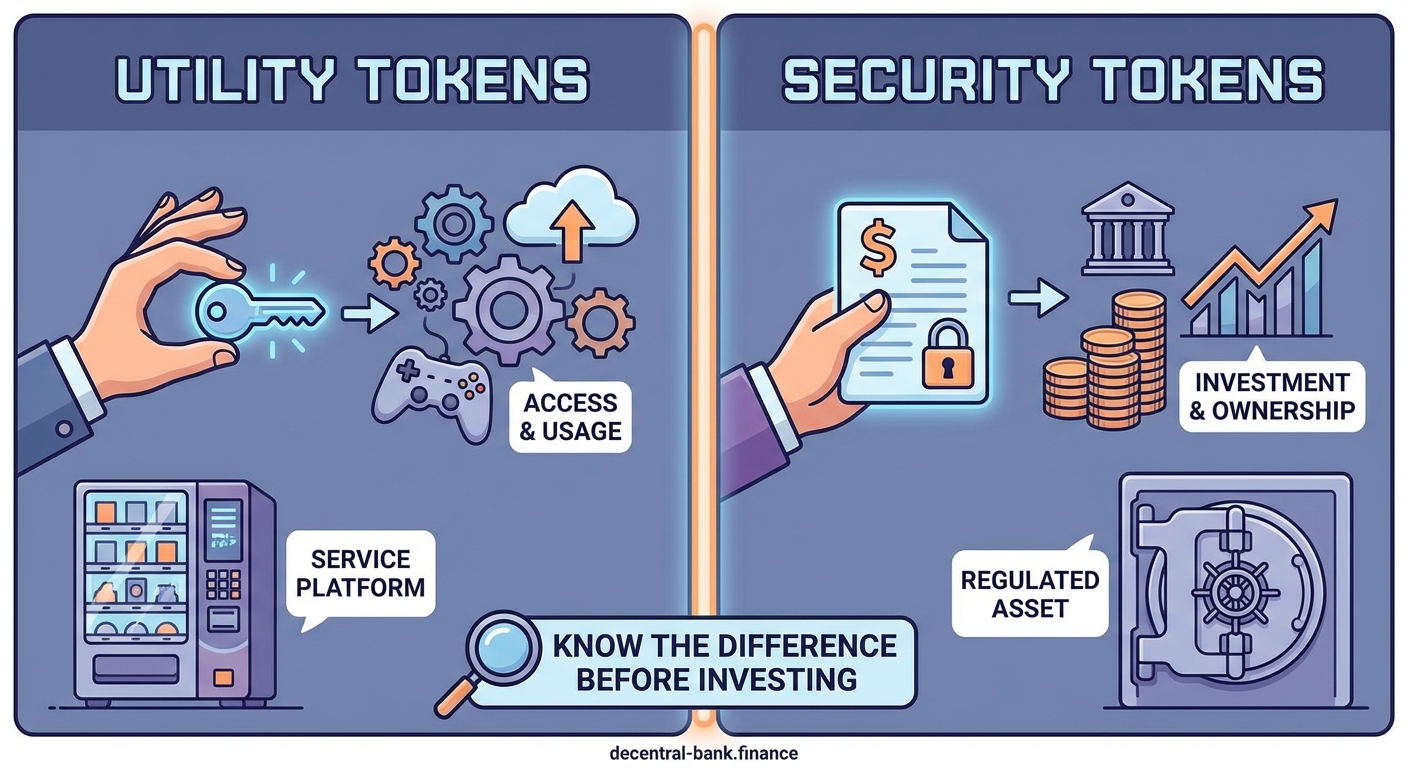
Governance token classification challenges
Determining whether governance tokens are securities became a critical issue in 2024.
The SEC’s framework evaluates several factors:
- Whether token holders expect profits from the efforts of others
- How much control token holders exercise over protocol operations
- Whether a identifiable development team makes key decisions
- How tokens were initially distributed and marketed
Protocols responded by restructuring governance to increase decentralization. Common changes included removing admin keys, distributing development responsibilities across multiple independent teams, and implementing time-locks on governance decisions.
Some projects conducted token buybacks to reduce circulation among passive holders. The theory holds that tokens held primarily by active governance participants look less like investment securities.
Legal opinions diverged on effectiveness. Some attorneys argue these changes create genuine decentralization. Others contend that regulatory agencies will look past structural changes to underlying economic realities.
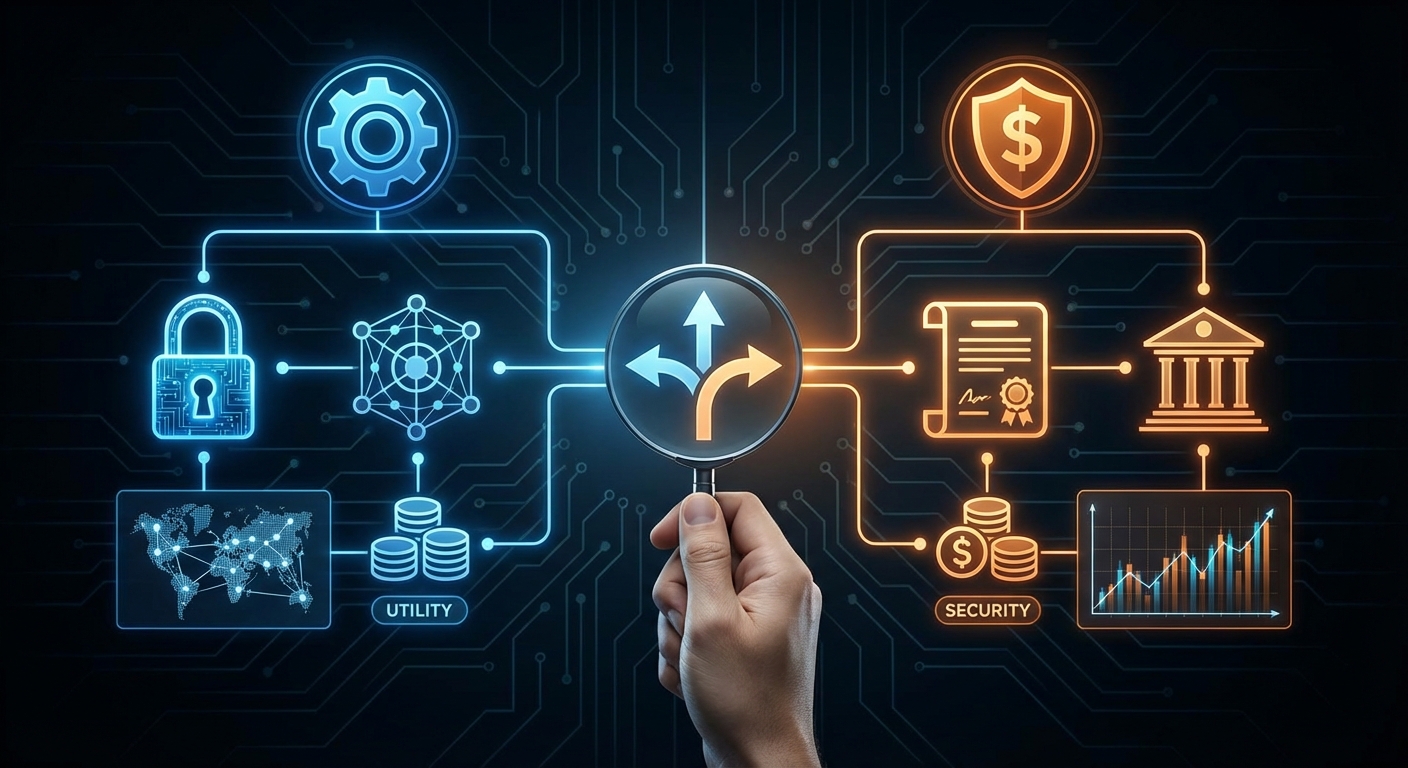
Compliance approaches comparison
| Approach | Implementation | Decentralization Level | Regulatory Risk | User Experience |
|---|---|---|---|---|
| Full KYC | Identity verification required for all users | Low | Very Low | Friction for new users |
| Tiered Access | KYC only for high-value transactions | Medium | Low | Balanced for most users |
| Compliant Frontend | Restrictions on official interface only | High | Medium | Technical users unaffected |
| Geographic Licensing | Different entities for different regions | Medium | Low | Varies by location |
| Zero-Knowledge Proofs | Privacy-preserving verification | High | Medium | Requires technical setup |
| No Compliance | Fully permission-less operation | Very High | Very High | Seamless but risky |
What developers are getting wrong
Several common compliance mistakes emerged in 2024.
Treating compliance as purely technical creates problems. Legal requirements involve ongoing monitoring, reporting, and policy updates. Implementing a KYC widget without establishing proper operational procedures fails to meet regulatory standards.
Assuming offshore incorporation provides complete protection proves mistaken. Regulators increasingly assert jurisdiction based on user location rather than entity registration. A Cayman Islands foundation doesn’t prevent enforcement if most users are in the United States.
Neglecting governance token holder liability exposes communities to risk. Token holders who vote on protocol decisions may face regulatory scrutiny, especially for decisions that facilitate illegal activity. Clear disclosures and liability limitations matter.
Copying compliance approaches without legal review causes issues. What works for one protocol in one jurisdiction may not apply elsewhere. Cookie-cutter solutions often miss critical jurisdiction-specific requirements.
The institutional adoption factor
Regulatory clarity accelerated institutional entry into DeFi throughout 2024.
Traditional financial institutions require legal certainty before deploying significant capital. Compliant DeFi protocols saw institutional total value locked increase by 340% in the first half of 2024, while non-compliant alternatives grew only 45%.
Asset managers launched DeFi-focused funds targeting accredited investors. These funds exclusively use protocols with clear regulatory status, robust compliance programs, and proper licensing. The capital influx benefits compliant protocols through deeper liquidity and lower volatility.
Banks began offering DeFi access to retail customers through compliant intermediaries. These services provide exposure to DeFi yields and applications while the bank handles compliance obligations. Users sacrifice some autonomy but gain legal protection and familiar interfaces.
Privacy coins and mixer protocols face scrutiny
Enhanced enforcement targeted privacy-focused DeFi applications in 2024.
Tornado Cash remained under sanction in most Western jurisdictions. Several developers faced ongoing legal proceedings. The situation created a chilling effect on privacy tool development.
New privacy protocols launched with built-in compliance features. These systems allow users to prove their funds don’t originate from illicit sources while maintaining transaction privacy. Adoption remained limited as users questioned whether privacy with compliance asterisks serves the original purpose.
Privacy-focused layer-2 solutions emerged as an alternative. These networks provide transaction privacy at the protocol level while maintaining the ability to prove compliance when needed. Regulatory acceptance varied by jurisdiction.
Decentralized exchanges adapt differently than lending protocols
Different DeFi categories faced different regulatory pressures.
Decentralized exchanges attracted the most regulatory attention. Most major DEXs implemented some form of compliance by mid-2024. The combination of high trading volumes and potential for wash trading or market manipulation made them enforcement priorities.
Lending protocols faced less immediate pressure. Regulators focused first on platforms that most closely resembled traditional financial services. Peer-to-peer lending with algorithmic interest rates presented novel questions that authorities approached more cautiously.
Derivatives protocols saw aggressive enforcement. Platforms offering leveraged trading, options, or futures faced requirements similar to traditional derivatives exchanges. Several shut down rather than comply with registration and capital requirements.
Yield aggregators operated in regulatory gray areas. These protocols automatically move user funds between different opportunities. Authorities debated whether they constitute investment advisors, requiring registration and fiduciary duties.
What users should consider now
The new regulatory environment requires users to make informed choices.
Assess your risk tolerance honestly. Compliant platforms offer legal clarity and consumer protections. Non-compliant alternatives provide greater privacy and freedom but carry regulatory risk. Your personal situation determines which trade-offs make sense.
Understand jurisdiction matters tremendously. The same protocol may be perfectly legal in one country and prohibited in another. Your physical location and tax residency create obligations regardless of where a protocol operates.
Diversification across compliance approaches reduces concentration risk. Using both compliant and decentralized platforms prevents complete loss of access if enforcement actions target one category.
Document everything for tax purposes. Regulatory clarity brings tax clarity. Authorities increasingly expect detailed reporting of DeFi transactions. Good records prevent problems during audits.
The path forward for decentralized finance
DeFi regulations 2024 marked a turning point rather than an ending.
Protocols that successfully balance compliance with decentralization will likely dominate the next market cycle. Pure decentralization maximalists face shrinking addressable markets as enforcement intensifies. Purely centralized platforms sacrifice the core innovations that made DeFi valuable.
The technology continues advancing faster than regulatory frameworks. Zero-knowledge proofs, decentralized identity, and privacy-preserving compliance tools enable new approaches that weren’t possible when current regulations were drafted.
International coordination remains incomplete. Arbitrage opportunities exist for protocols willing to navigate multiple jurisdictions. The lack of global standards creates complexity but also flexibility.
User education becomes critical. Understanding the compliance status, legal structure, and regulatory risks of protocols you use protects you from unexpected enforcement actions or platform shutdowns.
The regulatory frameworks introduced in 2024 will evolve as authorities see how initial approaches work in practice. Protocols, developers, and users who stay informed and adapt to changes will navigate this transition successfully. Those who ignore compliance realities or assume regulations will disappear face increasing challenges.