Imagine borrowing millions of dollars, manipulating an entire financial protocol, stealing hundreds of thousands in profit, and returning the loan within 13 seconds. No credit check. No collateral. No consequences if you fail.
That’s the reality of flash loan attacks in decentralized finance.
These exploits have drained over $500 million from DeFi protocols since 2020. They turn a legitimate DeFi feature into a weapon that can destabilize platforms and evaporate user funds in a single blockchain transaction.
Flash loan attacks exploit DeFi protocol vulnerabilities by borrowing massive amounts without collateral, manipulating prices or liquidity within a single transaction, then repaying the loan before the blockchain confirms it. Attackers profit from price discrepancies, oracle manipulation, or governance exploits while legitimate users suffer losses. Understanding these mechanics helps you identify risky protocols and protect your investments.
Understanding flash loans before the attacks
Flash loans represent one of DeFi’s most innovative features.
They let anyone borrow enormous sums of cryptocurrency without putting up collateral. The catch? You must return the entire loan plus fees within the same blockchain transaction.
If you can’t repay, the entire transaction reverts. It’s like it never happened.
Protocols like Aave, dYdX, and Uniswap offer flash loans for legitimate purposes. Arbitrage traders use them to profit from price differences across exchanges. Developers use them to refinance debt positions or swap collateral types.
The loan and repayment happen in seconds. One transaction block on Ethereum typically takes 12 to 15 seconds.
Here’s the problem: attackers discovered they could use this same mechanism to manipulate DeFi protocols faster than those systems could defend themselves.
How does DeFi actually work without banks or middlemen explains the foundational architecture that makes both flash loans and these attacks possible.
How attackers execute flash loan exploits
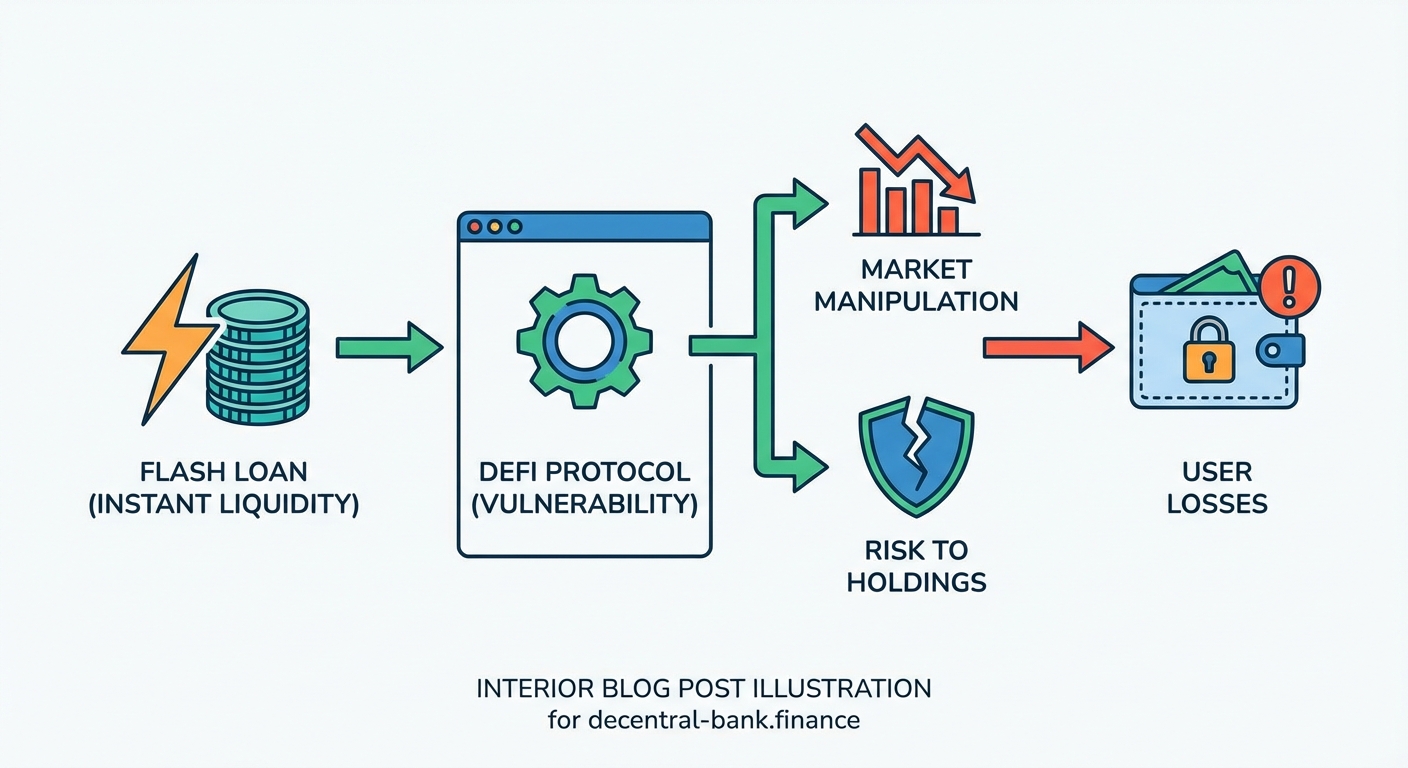
A flash loan attack follows a precise sequence.
Step 1: The attacker identifies a vulnerability in a DeFi protocol. Common weaknesses include reliance on a single price oracle, flawed governance mechanisms, or liquidity pool imbalances.
Step 2: They write a smart contract that automates the entire attack within one transaction.
Step 3: They borrow massive amounts of cryptocurrency using a flash loan. Often millions or tens of millions of dollars worth.
Step 4: They execute the exploit. This might involve manipulating token prices, draining liquidity pools, or exploiting calculation errors in lending protocols.
Step 5: They convert stolen assets and repay the flash loan with interest.
Step 6: They keep the profit, which can range from thousands to millions of dollars.
The entire sequence completes before the blockchain finalizes the transaction. If any step fails, the whole thing reverses and the attacker only loses gas fees.
This atomic execution makes flash loan attacks relatively low risk for attackers compared to traditional hacks.
Common attack vectors that drain protocols
Flash loan attackers exploit specific vulnerabilities repeatedly.
Price oracle manipulation
Many DeFi protocols rely on price oracles to determine asset values. Some protocols use a single decentralized exchange as their price source.
Attackers borrow funds, make massive trades on that specific exchange to artificially inflate or deflate prices, then exploit the manipulated price to borrow crypto without selling their assets at favorable rates or liquidate positions unfairly.
The PancakeBunny attack in May 2021 used this method. Attackers manipulated the price of BUNNY tokens, minted millions of tokens at the inflated price, then crashed the market by selling. Loss: $45 million.
Reentrancy exploits
Reentrancy attacks trick smart contracts into executing functions multiple times before updating their internal state.
An attacker borrows funds, calls a withdrawal function, and before that function completes, calls it again. The contract hasn’t registered the first withdrawal yet, so it processes the second one.
This repeats until the protocol is drained.
Liquidity pool imbalances
Protocols that provide liquidity on Uniswap without losing money face risks when attackers manipulate pool ratios.
By borrowing large amounts and making one-sided trades, attackers can create artificial imbalances. They then exploit arbitrage opportunities or trigger liquidations based on these distorted ratios.
Governance manipulation
Some attackers use flash loans to temporarily acquire voting power in governance tokens. They borrow tokens, vote on proposals that benefit them, execute those proposals, and return the tokens.
This happened with Beanstalk Farms in April 2022. An attacker used flash-loaned tokens to pass a governance proposal that sent $182 million to their wallet.
Real attacks that shocked the DeFi world
The numbers tell a sobering story.
| Protocol | Date | Amount Stolen | Attack Method |
|---|---|---|---|
| Euler Finance | March 2023 | $197 million | Donation attack exploiting contract logic |
| Cream Finance | October 2021 | $130 million | Price oracle manipulation |
| Beanstalk Farms | April 2022 | $182 million | Governance token flash loan |
| Alpha Homora | February 2021 | $37 million | Reentrancy and calculation error |
| Harvest Finance | October 2020 | $24 million | Arbitrage manipulation |
The Euler Finance attack stands out for its sophistication.
The attacker exploited a flaw in how the protocol handled donated collateral. They used flash loans to manipulate the donation mechanism, created artificial debt positions, and drained the protocol’s reserves.
Interestingly, the attacker returned the funds weeks later after negotiations with the Euler team and law enforcement. But that’s unusual. Most stolen funds never return.
“Flash loan attacks represent a unique category of exploit where the attack vector itself is a legitimate protocol feature. The challenge isn’t preventing flash loans but designing protocols that remain secure even when users can temporarily access unlimited capital.” — DeFi security researcher
Why these attacks keep succeeding
Flash loan attacks persist because they exploit fundamental design choices in DeFi.
Low barrier to entry: Anyone with basic smart contract knowledge can attempt an attack. No need to accumulate capital first.
Minimal risk: If the attack fails, the transaction reverts. The attacker only loses gas fees, typically a few hundred dollars.
High rewards: Successful attacks can net millions. The risk-reward ratio attracts sophisticated attackers.
Protocol complexity: Modern DeFi protocols interact with multiple other protocols. Each integration point creates potential vulnerabilities.
Speed advantage: Protocols can’t react within a single transaction. Traditional security measures like circuit breakers or admin interventions don’t work at this timescale.
The decentralized nature that makes DeFi work without banks or middlemen also means no central authority can halt suspicious transactions mid-flight.
Red flags that signal vulnerable protocols
Certain protocol characteristics correlate with flash loan attack risk.
- Single oracle dependency: Protocols using one price source for critical calculations face higher manipulation risk
- Unaudited smart contracts: Code that hasn’t undergone professional security audits often contains exploitable flaws
- Complex token mechanics: Protocols with rebasing tokens, elastic supplies, or unusual tokenomics create more attack surfaces
- Low liquidity: Small liquidity pools are easier to manipulate with borrowed funds
- Governance tokens with low market cap: Cheaper to acquire voting control via flash loans
- Rapid deployment: Protocols launched without extensive testing or gradual rollout
- Forked code without modification: Direct copies of other protocols may inherit known vulnerabilities
Before depositing funds in any DeFi protocol, check whether it addresses these risk factors.
How protocols defend against flash loan exploits
Developers have implemented several countermeasures.
Time-weighted average pricing (TWAP): Instead of using instantaneous prices, protocols average prices over multiple blocks. This makes single-transaction manipulation ineffective.
Multiple oracle sources: Chainlink and other oracle networks aggregate price data from numerous sources. Manipulating all of them simultaneously becomes prohibitively expensive.
Transaction size limits: Some protocols cap the maximum transaction size or implement progressive fees for large operations.
Multi-block requirements: Critical operations like governance votes or large withdrawals require multiple transactions across different blocks.
Circuit breakers: Automated systems that pause protocol functions when detecting unusual activity patterns.
Commit-reveal schemes: Users commit to an action in one transaction and execute it in a later transaction, preventing atomic exploitation.
Aave V3 introduced isolation mode, which limits how new or risky assets can interact with the broader protocol. This containment strategy prevents exploits from cascading across the entire system.
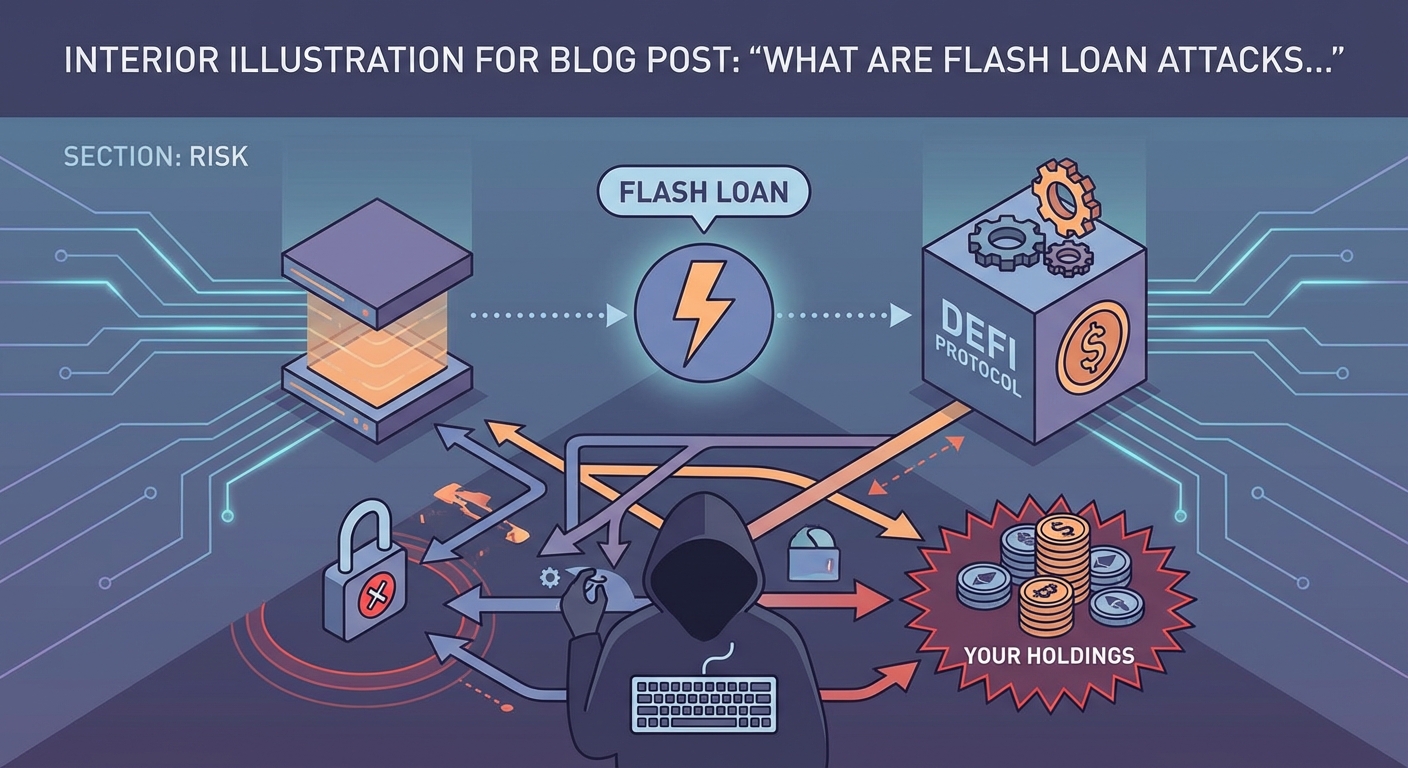
What you can do to protect your holdings
Individual users can’t prevent flash loan attacks, but you can minimize your exposure.
-
Research protocol security thoroughly. Check for completed audits from reputable firms like Trail of Bits, OpenZeppelin, or Consensys Diligence.
-
Diversify across protocols. Don’t concentrate holdings in a single platform, especially newer or experimental ones.
-
Understand the protocol’s oracle system. Platforms using Chainlink or multiple price feeds are generally safer than those relying on single DEX prices.
-
Monitor protocol governance. Watch for proposals that could introduce vulnerabilities or change security parameters.
-
Use protocols with insurance options. Some platforms offer coverage through Nexus Mutual or similar services.
-
Start small with new protocols. Test with amounts you can afford to lose before committing significant capital.
-
Keep funds in secure wallets when not actively using them. Choosing between hot wallets and cold wallets for your crypto reduces your exposure window.
The protection strategies for DeFi rug pulls and exit scams also apply to flash loan attack risk assessment.
The legitimate uses worth preserving
Flash loans aren’t inherently malicious.
Legitimate traders use them for arbitrage. When Bitcoin trades at $50,000 on one exchange and $50,200 on another, a trader can borrow funds, buy low, sell high, repay the loan, and pocket the difference.
This activity actually improves market efficiency by eliminating price discrepancies.
Developers use flash loans to refinance positions. If you have a loan on one platform at 8% interest and another platform offers 5%, you can use a flash loan to pay off the first loan, open a new position on the second platform, and reduce your interest costs.
All without needing capital upfront.
Smart contract developers use flash loans to test their code under extreme conditions. By simulating massive capital flows, they can identify vulnerabilities before attackers do.
The challenge is preserving these benefits while preventing exploitation.
Regulatory attention and protocol evolution
Flash loan attacks have attracted regulatory scrutiny.
The SEC and other financial regulators view these exploits as evidence that DeFi needs stronger oversight. How major DeFi protocols are responding to new regulatory frameworks in 2024 shows the industry adapting to increased attention.
Some argue that flash loan attacks constitute market manipulation under existing securities law. Others contend they’re simply exploiting poor code, which isn’t illegal.
The legal ambiguity creates uncertainty for both attackers and protocol developers.
Meanwhile, protocol design continues evolving. Newer platforms build in flash loan resistance from the ground up rather than adding it as an afterthought.
Cross-chain bridges represent the next frontier. As DeFi expands across multiple blockchains, attackers are finding ways to use flash loans on one chain to exploit protocols on another.
Distinguishing attacks from other DeFi risks
Flash loan attacks differ from other threats you might encounter.
Rug pulls involve developers intentionally abandoning projects and stealing funds. Flash loan attacks exploit technical vulnerabilities, often without insider involvement.
Smart contract bugs can drain protocols, but they don’t necessarily involve flash loans. The DAO hack in 2016 used a reentrancy exploit but didn’t involve borrowed funds.
Phishing attacks target individual users through fake websites or social engineering. Flash loan attacks target protocol-level vulnerabilities.
Understanding these distinctions helps you assess different risk categories and apply appropriate protective measures.
The security mindset for DeFi participation
Participating in DeFi requires accepting certain risks.
No protocol is completely immune to flash loan attacks. Even audited, established platforms have fallen victim when attackers discovered novel exploit combinations.
The key is understanding what you’re getting into.
When you start staking crypto or provide liquidity, you’re trusting that the protocol’s smart contracts work as intended under all conditions, including extreme scenarios like flash loan attacks.
That trust should be informed, not blind.
Read audit reports. Understand the protocol’s security measures. Know the team’s track record. Recognize warning signs.
The same due diligence that helps you identify utility tokens vs security tokens before investing applies to evaluating protocol security.
Why understanding beats fear
Flash loan attacks sound terrifying when you first learn about them.
Millions stolen in seconds. Complex exploits. Technical vulnerabilities. It’s enough to make anyone avoid DeFi entirely.
But understanding how these attacks work actually reduces anxiety.
You learn which protocols implement proper safeguards. You recognize red flags before depositing funds. You understand that not all DeFi platforms carry equal risk.
Knowledge transforms vague fear into specific, manageable risk assessment.
The attackers who execute these exploits aren’t magical. They’re identifying logical flaws in code and exploiting them systematically. When protocols address those flaws through better oracle systems, multi-block requirements, and robust testing, they become significantly more secure.
Your job as a user is to favor protocols that take security seriously over those chasing the highest yields without proper safeguards.
Moving forward with eyes open
Flash loan attacks will continue as long as DeFi exists.
They’re a consequence of permissionless, composable finance. The same properties that let anyone access financial services without gatekeepers also let attackers access enormous capital without permission.
The solution isn’t eliminating flash loans. It’s building protocols resilient enough to withstand them.
As a DeFi user, you benefit from this ongoing security evolution. Each successful attack teaches the community something new. Protocols patch vulnerabilities. Security practices improve. The ecosystem becomes more robust.
Your role is staying informed, choosing platforms wisely, and never investing more than you can afford to lose in experimental protocols. Flash loan attacks are serious, but they don’t have to keep you out of DeFi entirely. They should make you more careful about where you participate.





