You connect your wallet to a new DeFi protocol. A popup appears asking you to approve access to your tokens. You click confirm, and suddenly that protocol can interact with your funds. But what actually happened behind the scenes?
When you approve a smart contract, you grant it permission to move specific tokens from your wallet on your behalf. This approval is recorded on the blockchain through the ERC-20 approve function, which sets a spending limit. The contract can then transfer tokens up to that limit without asking again. Understanding this process helps you manage permissions safely and revoke unnecessary access to protect your assets.
The technical process of token approvals
Token approvals work through a standardized function built into most cryptocurrency tokens. When you approve a smart contract, your wallet sends a transaction to the token contract itself, not to the DeFi protocol you’re using.
This transaction calls the approve function with two key pieces of information. First, the address of the smart contract receiving permission. Second, the amount of tokens it can spend.
The token contract records this permission in its internal ledger. Think of it like giving someone a limited power of attorney over a specific bank account. They can withdraw up to the approved amount, but they can’t touch anything else in your wallet.
Most wallets show you these details before you confirm. You’ll see which token you’re approving, which contract is receiving permission, and how many tokens are included in the allowance.
The blockchain permanently records this approval transaction. Anyone can verify it by checking your wallet’s approval history on a block explorer.
Why DeFi protocols need your approval
Smart contracts can’t just take tokens from your wallet. The blockchain’s security model prevents unauthorized transfers as a fundamental protection.
When you want to trade on a decentralized exchange, the exchange’s smart contract needs permission to move your tokens into its liquidity pools. Without an approval, the trade transaction would fail.
Lending protocols need approval to deposit your tokens as collateral. Staking platforms need it to lock your tokens in their contracts. Yield farming strategies need it to move tokens between different protocols.
This permission system creates a trade-off. It protects your assets from random contracts trying to steal funds. But it also means you must explicitly grant access to legitimate protocols you want to use.
The approval happens separately from the actual token transfer. You approve once, then the protocol can execute multiple transfers within that allowance. This saves gas fees compared to requesting permission for every single transaction.
Understanding approval amounts
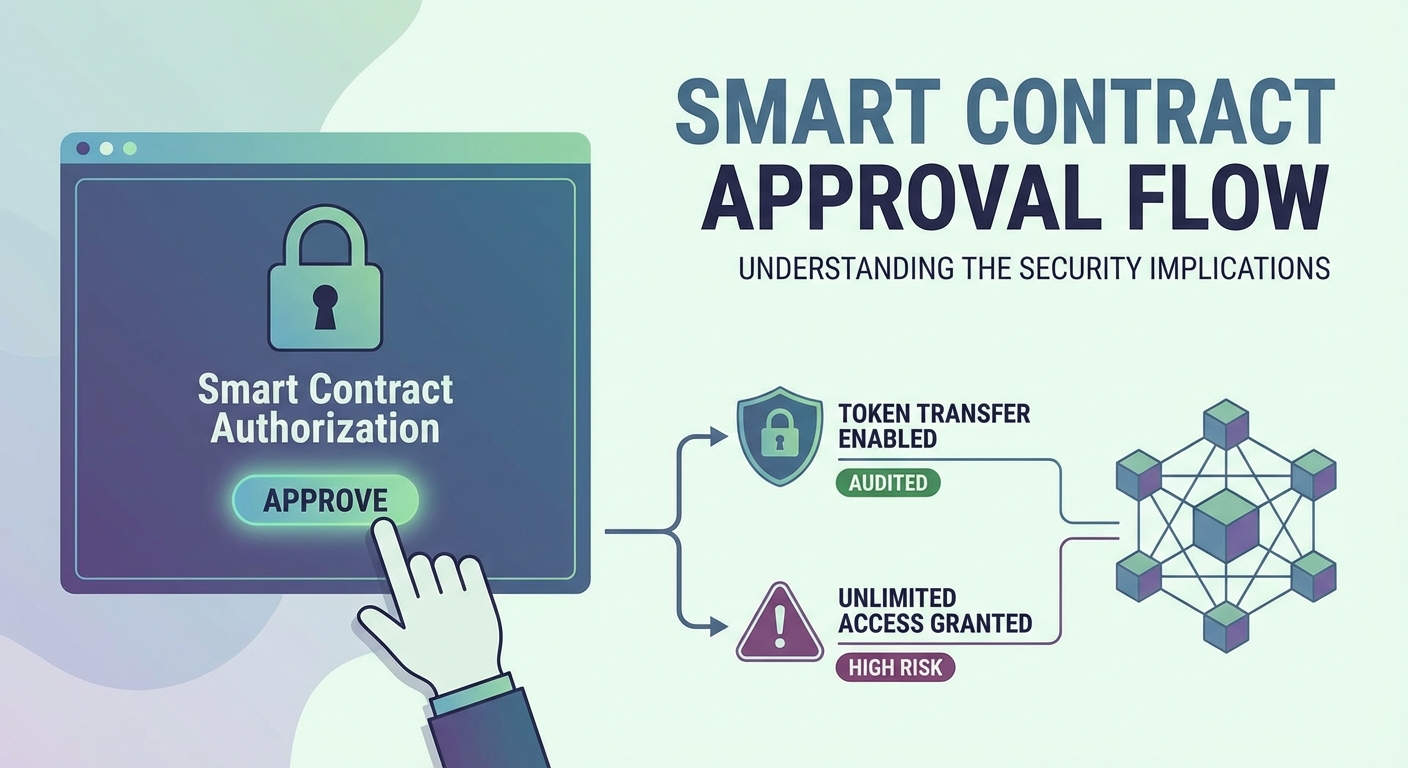
When approving a smart contract, you typically see two options: approve a specific amount or approve unlimited tokens.
Many wallet interfaces default to unlimited approvals. The number often appears as a massive figure with dozens of zeros. This represents the maximum possible value the token contract can handle.
Unlimited approvals offer convenience. You approve once and never need to approve that token for that contract again. You can make multiple trades, deposits, or transfers without additional approval transactions.
But unlimited approvals carry security risks. If the protocol gets hacked or contains malicious code, the attacker can drain all tokens you’ve approved, not just the amount you intended to use immediately.
Limited approvals restrict the contract to a specific amount. You might approve exactly 100 USDC for a single trade. Once the contract uses those 100 USDC, it can’t access any more without a new approval.
This approach requires more transactions and higher gas fees over time. Each time you want to interact with the protocol beyond your current allowance, you need another approval.
Here’s how different approval strategies compare:
| Strategy | Security Level | Convenience | Gas Cost | Best For |
|---|---|---|---|---|
| Unlimited approval | Lower | High | One-time | Trusted protocols you use frequently |
| Exact amount | Highest | Low | Repeated | New or unfamiliar protocols |
| Moderate buffer | Medium | Medium | Occasional | Regular use with caution |
| Revoke after use | Highest | Lowest | Highest | One-time interactions |
What the smart contract can and cannot do
An approved smart contract gains specific, limited permissions. It can transfer tokens from your wallet up to the approved amount. That’s the extent of its power.
The contract cannot:
- Access tokens you didn’t approve
- Move different tokens without separate approvals
- Withdraw ETH or native blockchain tokens (these don’t require approvals)
- Change your wallet’s private keys
- Approve other contracts on your behalf
- Access tokens you receive after the approval
The approval only affects the specific token you approved. If you approved USDC, the contract can’t touch your ETH, DAI, or any other tokens.
The contract can only pull tokens when its code executes. If you approved a decentralized exchange, it can only take tokens during a trade transaction you initiate. It can’t randomly decide to transfer tokens at any time.
However, malicious contracts can be designed to drain approved tokens the moment you interact with them in any way. This is why vetting contracts before approval matters so much.
Before approving any smart contract, verify its address matches the official protocol documentation. Scammers create fake interfaces that request approvals for malicious contracts designed to steal your tokens immediately.
The security risks you’re accepting
Every approval creates a potential vulnerability. Even legitimate protocols can become security risks through various attack vectors.
Smart contract bugs represent one major risk. A coding error might allow attackers to exploit the contract and drain all approved tokens from users. Major DeFi hacks have occurred this way, affecting even well-audited protocols.
Malicious upgrades pose another threat. Some protocols use upgradeable contracts that developers can modify. If the development team turns malicious or gets compromised, they could upgrade the contract to steal approved funds.
Phishing attacks trick users into approving malicious contracts. A fake website might look identical to a real protocol but connect your wallet to a scam contract. Once approved, it immediately drains your tokens.
Frontend compromises happen when attackers hack a protocol’s website. They modify the interface to request approvals for their own malicious contracts instead of the real protocol.
Approval farming scams promise rewards for connecting your wallet and approving their contract. Once approved, they steal everything you authorized.
The risk persists as long as the approval exists. Even if you stop using a protocol, your old approvals remain active unless you manually revoke them.
How to check your existing approvals
Your wallet likely has dozens or hundreds of active approvals you’ve forgotten about. Each one represents a potential security risk.
Several tools let you view all approvals associated with your wallet address:
- Connect your wallet to an approval management platform
- The tool scans the blockchain for all approval transactions from your address
- It displays a list showing which contracts can access which tokens
- You can see the approved amounts and when you granted each permission
Popular approval checkers include Revoke.cash, Etherscan’s token approval checker, and Unrekt. These platforms support multiple blockchains including Ethereum, Binance Smart Chain, Polygon, and others.
The interface typically shows the token name, the contract address with permission, the approved amount, and options to revoke. Some tools estimate the dollar value at risk for each approval.
Checking approvals regularly should become part of your security routine. Monthly reviews help you identify and remove permissions you no longer need.
Pay special attention to approvals for:
- Protocols you haven’t used in months
- Projects that have shut down or been abandoned
- Contracts with unlimited allowances
- Unfamiliar addresses you don’t recognize
Revoking approvals you no longer need
Removing unnecessary approvals reduces your attack surface. The process mirrors how you granted approval originally.
To revoke an approval:
- Use an approval management tool or your token contract directly
- Submit a revoke transaction that sets the approval amount to zero
- Pay gas fees to execute the transaction
- Confirm the approval no longer appears in your active permissions
Some wallets include built-in approval management features. MetaMask, for example, lets you view and revoke token permissions directly in the interface.
Revoking costs gas fees, which can add up if you’re removing many approvals. Consider prioritizing based on risk. Revoke unlimited approvals first, especially for lesser-known protocols.
You might choose to keep approvals active for protocols you use regularly and trust deeply. Major platforms like Uniswap or Aave that have operated securely for years present lower risk than new protocols.
But even trusted protocols can be compromised. If you’re not actively using a protocol, revoking its approval makes sense regardless of its reputation.
Some users revoke approvals immediately after completing transactions. This maximizes security but significantly increases gas costs. Balance your security needs against practical usability.
Best practices for safer approvals
Smart approval habits protect your funds without completely avoiding DeFi protocols.
Always verify the contract address before approving. Check the official protocol documentation or verified social media accounts. One wrong character in an address means you’re approving a completely different contract.
Start with limited approvals for new protocols. Approve only what you need for your immediate transaction. You can always approve more later if the protocol proves trustworthy.
Research protocols before using them. Check for security audits, track record, and community reputation. Avoid protocols that launched recently without audits or those with anonymous teams.
Use separate wallets for different risk levels. Keep large holdings in a wallet that never approves contracts. Use a different wallet with smaller amounts for DeFi interactions.
Enable transaction simulation if your wallet supports it. Tools like Tenderly or Pocket Universe show you what will happen before you sign, including unexpected token transfers.
Read approval requests carefully. Don’t click through popups automatically. Verify the token, amount, and contract address match what you expect.
Set calendar reminders to review your approvals monthly. This habit catches forgotten permissions before they become security issues.
Consider these approval safety levels:
- High security: Limited approvals, immediate revocation, separate wallet
- Medium security: Moderate approvals for trusted protocols, quarterly reviews
- Low security: Unlimited approvals, no revocations, single wallet for everything
The level you choose depends on your holdings, risk tolerance, and how actively you use DeFi.
What happens after you approve
Once your approval transaction confirms, the smart contract can interact with your tokens according to the permission you granted.
The next time you use that protocol, you won’t see an approval request for that token. The protocol will directly execute the token transfer as part of your action.
For example, after approving USDC on Uniswap, your next swap transaction only needs one signature. Uniswap’s contract transfers your USDC and sends you the output token in a single transaction.
The approval remains active indefinitely. There’s no expiration date unless the token contract implements time-limited approvals (rare). Your approval from years ago still works today unless you revoked it.
You can monitor approval usage through block explorers. Search for your wallet address and filter for token transfer events. You’ll see when approved contracts actually moved your tokens.
Some protocols never use their full approval amount. You might approve 1,000 tokens but only ever trade 100. The contract retains permission for the remaining 900 until you revoke it.
Other users’ approvals don’t affect yours. Even if a protocol gets hacked and drains tokens from thousands of users, only wallets that previously approved that contract are at risk.
Common mistakes people make
Many users approve contracts without understanding the implications. These errors create unnecessary security risks.
Approving unlimited amounts by default happens constantly. Users click through wallet popups without reading them, accepting whatever amount the interface suggests.
Ignoring contract addresses is another frequent mistake. People assume the website they’re on connects to the legitimate contract, but phishing sites exploit this assumption.
Never revoking old approvals leaves wallets exposed. Users accumulate hundreds of active permissions over time, each representing a potential vulnerability.
Approving contracts on unfamiliar blockchains without adjusting security practices. The same approval risks exist on every chain, but users often treat new networks more casually.
Using the same wallet for everything combines high-value holdings with active DeFi use. This puts your entire portfolio at risk from a single malicious approval.
Trusting protocol interfaces blindly. Even legitimate websites can be compromised. Always verify contract addresses through multiple sources.
Skipping research on new protocols. Users approve contracts for projects they discovered minutes earlier, without checking audits or community feedback.
Making informed approval decisions
Every approval requires a risk assessment. Before clicking confirm, ask yourself several questions.
Do you trust this protocol? Consider its track record, audit history, and team reputation. Newer protocols carry higher risk than established platforms.
How much value are you approving? The potential loss should match your risk tolerance. Approving $50 worth of tokens differs from approving $50,000.
How often will you use this protocol? Frequent use might justify unlimited approvals for convenience. One-time interactions should use exact amounts.
What’s the worst-case scenario? If this contract gets hacked or turns malicious, how much could you lose? Only approve amounts you can afford to lose.
Can you reduce the approval amount? Many interfaces default to unlimited but allow you to change the amount before confirming.
Is this the official contract? Verify the address matches documentation from trusted sources, not just the website you’re currently viewing.
These questions take seconds to consider but can prevent costly mistakes. Treat each approval as a serious security decision, not a routine popup to dismiss.
Protecting yourself going forward
Smart contract approvals enable DeFi participation but require ongoing security awareness. The permission you grant today remains active until you explicitly revoke it.
Regular approval audits should become part of your crypto security routine. Monthly reviews help you identify and remove unnecessary permissions before they become vulnerabilities.
Stay informed about security incidents in protocols you’ve approved. Follow project announcements and security researchers who report vulnerabilities. If a protocol you’ve approved gets compromised, revoke access immediately.
Your approval strategy should match your security needs. High-value wallets deserve conservative approval practices. Experimental wallets for trying new protocols can accept more risk.
Understanding what happens when you approve a smart contract empowers you to use DeFi safely. You’re not blindly trusting protocols. You’re making informed decisions about which contracts deserve access to your tokens and for how much.
The blockchain’s permission system protects you by default. Contracts can’t touch your tokens without approval. But once you grant that approval, responsibility shifts to you. Choose wisely, monitor actively, and revoke promptly when permissions are no longer needed.





