You own $50,000 in crypto, and it sits in a wallet controlled by a single password. One phishing link, one compromised device, one moment of carelessness, and it’s gone forever. No bank will reverse the transaction. No customer service team can help you.
This is where multi-signature wallets change everything.
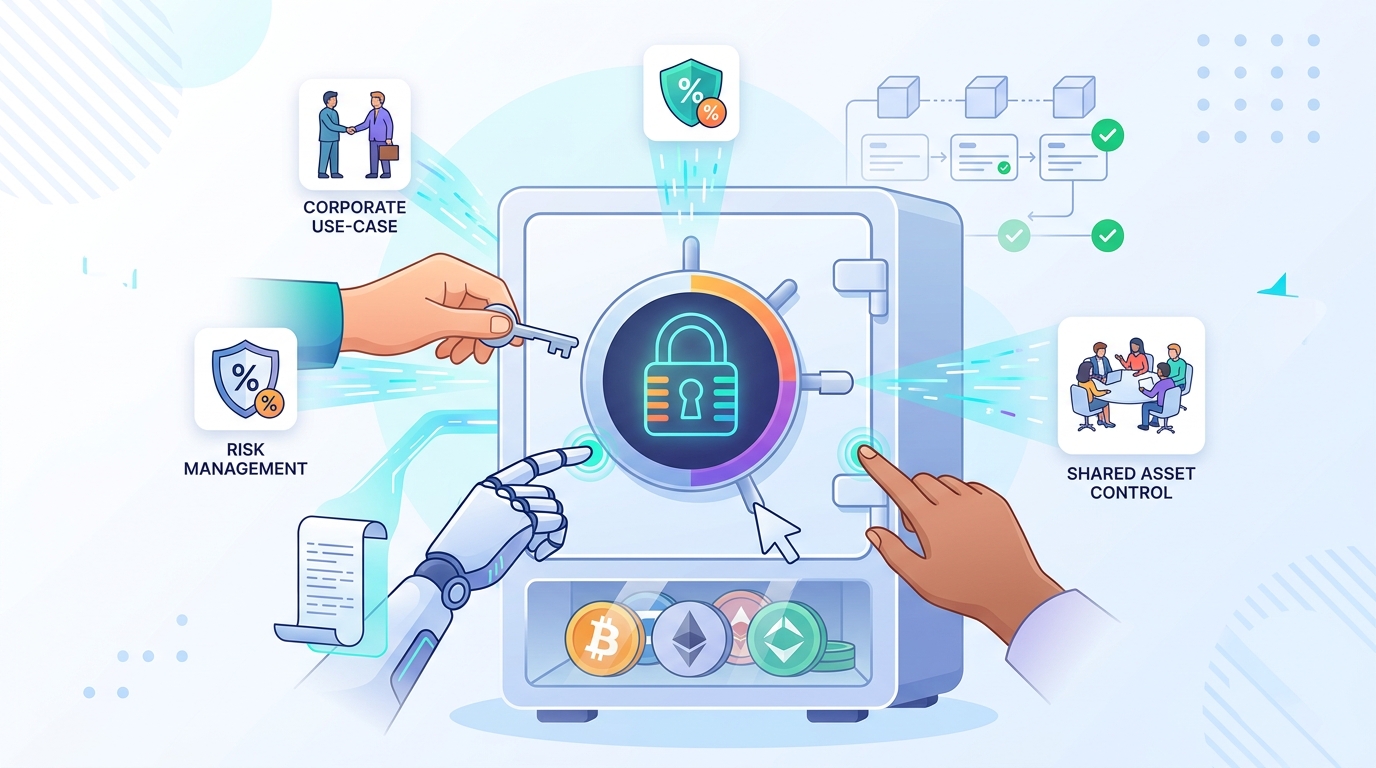
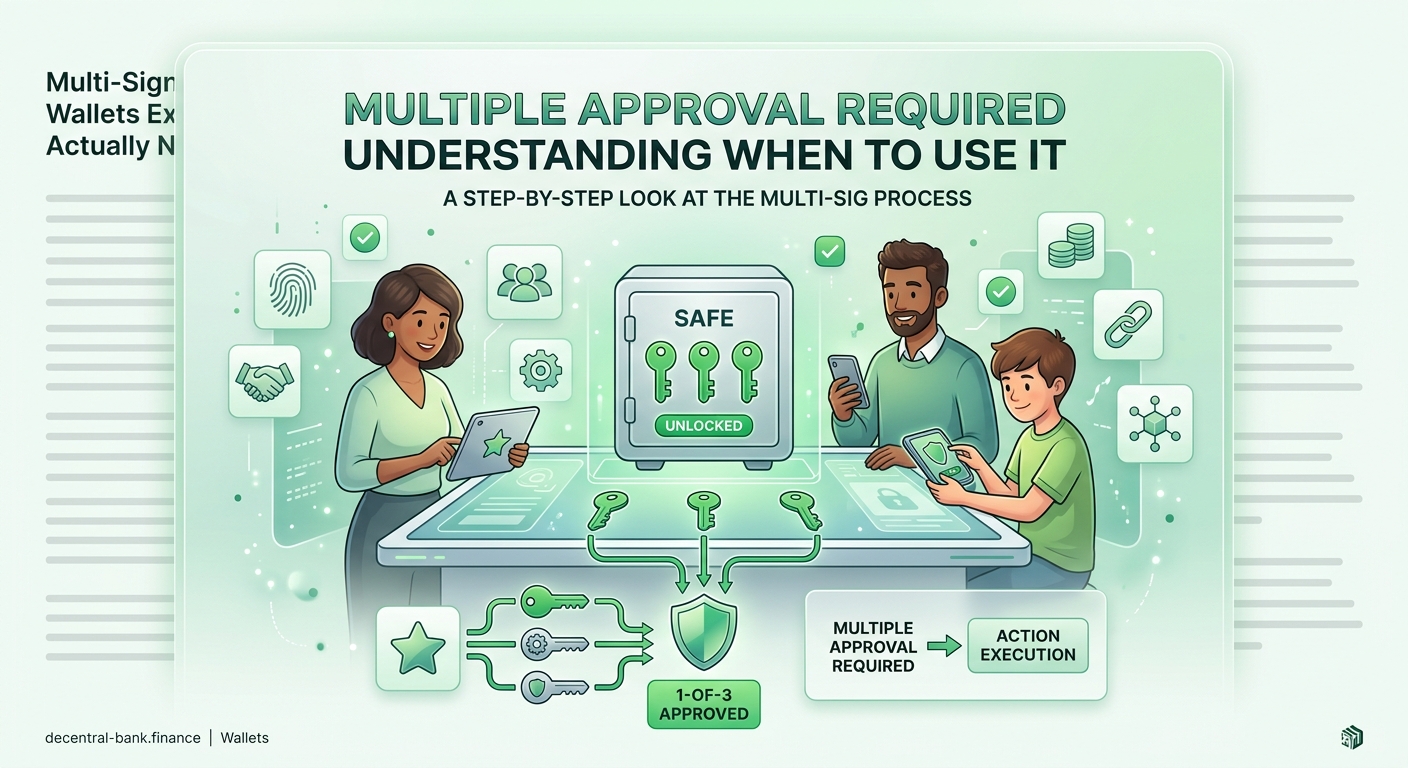
A multisig wallet requires multiple private keys to authorize transactions, distributing control across several people or devices. Instead of one person holding complete access, you might need 2 out of 3 signatures or 3 out of 5 to move funds. This protects against theft, loss, and single points of failure while enabling shared treasury management for businesses and DAOs.
Understanding multi-signature wallets from the ground up
A multi-signature wallet (multisig) functions like a bank vault that needs multiple keys to open.
Traditional crypto wallets use one private key. If someone gets that key, they control everything. A multisig wallet splits this control across multiple keys, requiring a predetermined number to approve any transaction.
Think of it like a business checking account that requires two signatures on checks above $10,000. The bank won’t process the payment unless both the CEO and CFO sign. Multisig wallets apply this same principle to cryptocurrency.
The setup looks like this: you create a wallet requiring M signatures out of N total keys. Common configurations include 2-of-3, 3-of-5, or 2-of-2. The numbers depend on your security needs and convenience preferences.
Here’s a real example. You set up a 2-of-3 multisig wallet. You hold one key on your hardware wallet. Your spouse holds another key on their phone. A trusted friend stores the third key offline. To spend funds, any two of you must approve the transaction.
If someone steals your hardware wallet, they can’t move your crypto without a second signature. If you lose your key entirely, your spouse and friend can still recover the funds together.
How multisig wallets actually work behind the scenes
The technical foundation sits at the blockchain level, not in any single app or device.
When you create a multisig wallet, you’re creating a special type of address governed by smart contract rules (on chains like Ethereum) or native script functionality (on Bitcoin). These rules specify exactly how many signatures the network needs before executing a transaction.
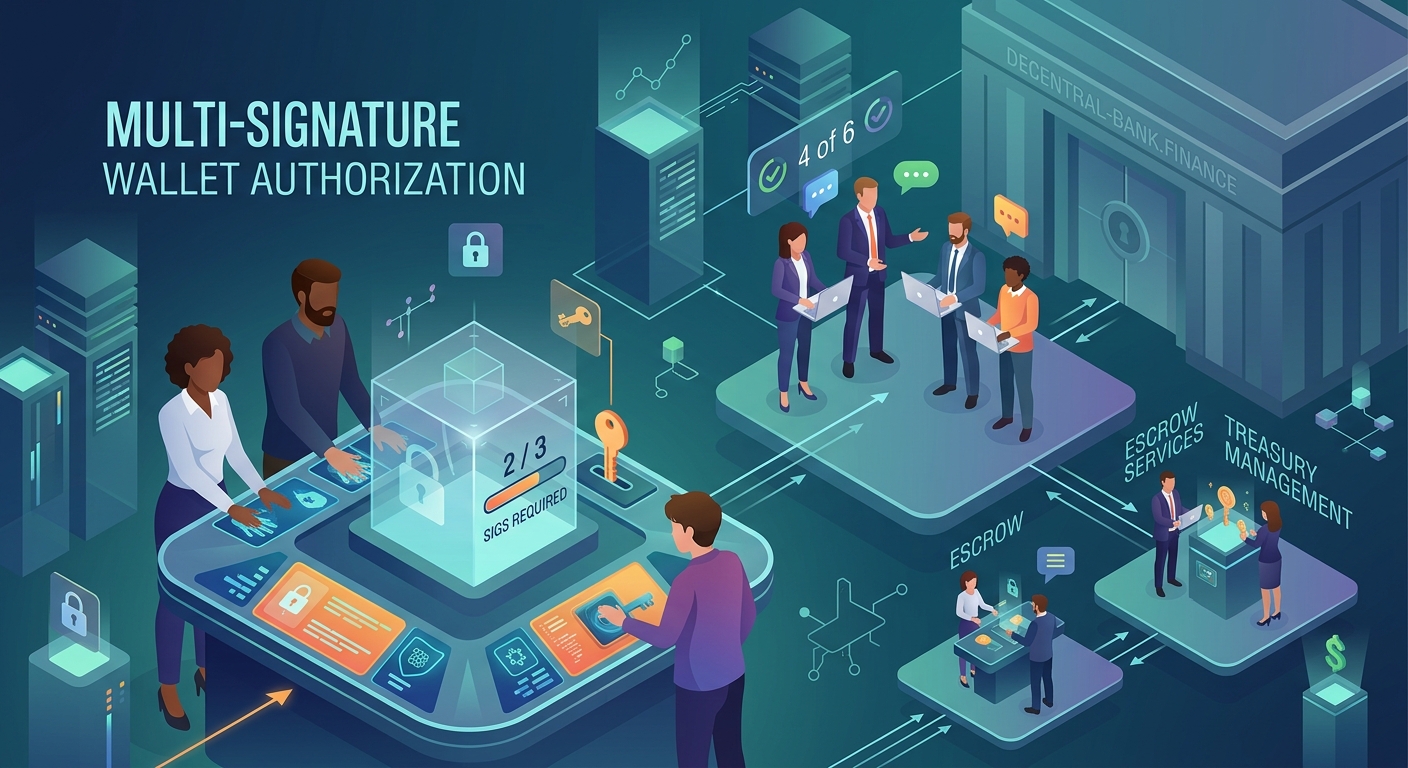
Let’s walk through a Bitcoin multisig transaction:
- You initiate a transaction from your multisig address
- You sign it with your private key, creating the first signature
- The partially signed transaction gets shared with other keyholders
- Each required party adds their signature
- Once the threshold is met, the transaction broadcasts to the network
- Miners validate that all signatures are legitimate and execute the transfer
The blockchain itself enforces these rules. No central authority can override them. No support team can bypass the signature requirements.
Different blockchains implement multisig differently. Bitcoin uses Pay-to-Script-Hash (P2SH) or Pay-to-Witness-Script-Hash (P2WSH) addresses. Ethereum relies on smart contracts like those from Gnosis Safe or Safe (formerly Gnosis Safe).
The user experience varies by platform, but the security principle remains constant: distributed control prevents single points of failure.
Who actually needs a multisig wallet
Not everyone benefits equally from multisig complexity. The technology makes sense for specific situations where the security benefits outweigh the convenience tradeoffs.
Business treasuries and DAOs
Any organization managing shared funds should use multisig wallets. A startup holding $200,000 in crypto shouldn’t trust one person with complete access. A 3-of-5 setup with the CEO, CFO, CTO, and two board members prevents both internal theft and external hacks.
Decentralized autonomous organizations (DAOs) managing millions in community funds almost universally use multisig wallets. When you participate in how DeFi actually works without banks or middlemen, you’ll notice that serious protocols protect treasury funds with multisig controls requiring multiple core team members or elected representatives to approve spending.
High-net-worth individuals
If you hold more than $100,000 in crypto, multisig deserves serious consideration. The risk of total loss from a single compromised device becomes unacceptable at these amounts.
A 2-of-3 setup with one key on a hardware wallet, another on a different hardware wallet stored separately, and a third with a trusted family member or attorney provides robust protection without excessive complexity.
Couples managing joint crypto holdings
Married couples or partners with significant shared crypto assets benefit from 2-of-2 multisig wallets. Neither person can unilaterally move funds, preventing disputes and protecting both parties.
The arrangement also solves inheritance problems. If one partner passes away, the surviving partner still has their key and can work with the estate to access the second key.
Anyone worried about the $5 wrench attack
Physical coercion represents a real threat for known crypto holders. If someone forces you to hand over your private key, a single-signature wallet offers no protection.
With a 2-of-3 multisig, you can honestly say “I can’t access the funds alone.” The attacker would need to locate and coerce multiple keyholders, dramatically increasing their risk and reducing the attack’s viability.
Common multisig configurations and their tradeoffs
Different signature thresholds serve different purposes. Choosing the right configuration requires balancing security against usability.
| Configuration | Best For | Security Level | Convenience | Single Point of Failure |
|---|---|---|---|---|
| 2-of-2 | Couples, small partnerships | Medium | Low | Yes (both keys required) |
| 2-of-3 | Individuals, small teams | High | Medium | No |
| 3-of-5 | Businesses, DAOs | Very High | Medium | No |
| 4-of-7 | Large organizations | Extremely High | Low | No |
The 2-of-2 configuration
This setup requires both keyholders to approve every transaction. It works well for equal partnerships but creates problems if either keyholder becomes unavailable.
If your business partner goes on a month-long expedition to Antarctica with no internet, you can’t access shared funds until they return. If either key is permanently lost, the funds become unrecoverable.
Use 2-of-2 only when both parties need equal control and both will remain consistently available.
The 2-of-3 sweet spot
Most individual users and small teams find 2-of-3 optimal. You maintain security against single key compromise while avoiding complete lockout if one key is lost.
You might distribute keys like this:
– Key 1: Your primary hardware wallet
– Key 2: A backup hardware wallet in a safe deposit box
– Key 3: A trusted family member or attorney
To spend funds normally, you use Keys 1 and 2. If your house burns down destroying Key 1, you can still access funds with Keys 2 and 3. If the family member loses Key 3, you don’t care because you have Keys 1 and 2.
The 3-of-5 business standard
Organizations with multiple stakeholders typically use 3-of-5 or higher thresholds. This prevents any two people from colluding to steal funds while maintaining accessibility if one or two keyholders become unavailable.
A typical setup for a crypto startup:
– CEO holds one key
– CFO holds one key
– CTO holds one key
– Board member A holds one key
– Board member B holds one key
Any three can approve transactions. If the CTO quits and refuses to participate, the other four can still operate. If two people conspire to steal funds, they can’t succeed without a third signature.
Setting up your first multisig wallet step by step
The process varies by platform, but the fundamental steps remain consistent across implementations.
- Choose your platform
For Ethereum and EVM-compatible chains, Safe (formerly Gnosis Safe) dominates the multisig space. For Bitcoin, Electrum, Sparrow Wallet, and Specter Desktop offer robust multisig support.
Your choice depends on which blockchains you use and whether you need mobile access or prefer desktop-only security.
- Decide on your configuration
Determine how many total keys (N) and how many required signatures (M) your setup needs. Start conservative. You can always create a new wallet with different parameters, but you can’t change an existing multisig configuration.
- Generate your keys
Each keyholder generates their own private key, ideally on separate hardware wallets or secure devices. Never generate all keys on a single device, as this defeats the entire purpose of multisig security.
For a 2-of-3 setup, you might use two different hardware wallet brands plus a mobile wallet, ensuring no single device compromise affects multiple keys.
- Create the multisig address
Using your chosen platform, input all public keys (not private keys) and specify your M-of-N threshold. The platform generates a unique multisig address.
This address looks different from standard addresses. On Bitcoin, it often starts with “3” or “bc1” (for P2WSH). On Ethereum, it’s a contract address.
- Test with a small amount
Send $20 worth of crypto to your new multisig address. Then practice the withdrawal process, ensuring all keyholders can access their keys and successfully sign a transaction.
Many people skip this step and later discover they misconfigured something. Testing with trivial amounts prevents expensive mistakes.
- Document your setup
Write down which keys are stored where, what the signature threshold is, and how to initiate transactions. Store this documentation separately from the keys themselves.
If you become incapacitated, your family needs to understand how to access the funds. Clear documentation makes this possible.
Mistakes people make with multisig wallets
The technology provides excellent security, but only when used correctly. These errors undermine the benefits and sometimes create worse situations than single-signature wallets.
Storing multiple keys in the same location
Keeping two keys from a 2-of-3 setup in your home safe defeats the purpose. A burglar who steals your safe gets enough keys to drain the wallet.
Distribute keys geographically. One in your home, one in a bank safe deposit box, one with a trusted person in another city.
Losing track of key locations
You set up a 3-of-5 multisig three years ago. Now you can only locate two keys. The other three are somewhere in storage boxes from your last move, on old phones you donated, or with people you’ve lost contact with.
Maintain a secure registry of key locations. Update it whenever you move a key or change keyholders. Review it annually.
Using the same seed phrase across multiple keys
Some people generate multiple keys from the same seed phrase, thinking this provides backup. This completely eliminates multisig security because anyone with that seed phrase controls multiple keys.
Each key must derive from an independent seed phrase, generated on separate devices.
Choosing keyholders who can’t handle the responsibility
Your elderly parent who struggles with email probably shouldn’t hold a key to your $500,000 crypto treasury. Your friend who loses their phone twice a year isn’t a good choice either.
Select keyholders based on technical competence, reliability, and geographic distribution. Sometimes a professional service makes more sense than well-meaning but unreliable friends.
Forgetting about transaction fees
Multisig transactions cost more in network fees than standard transactions because they contain more data (multiple signatures). On Bitcoin during high-fee periods, multisig transactions can cost 2-3x more.
Budget for higher transaction costs. If you’re optimizing for minimum fees, multisig adds friction you might not want.
Multisig wallets for different cryptocurrencies
Implementation quality varies significantly across blockchains. Some chains have mature, battle-tested multisig solutions. Others offer experimental or limited options.
Bitcoin multisig
Bitcoin has supported multisig since 2012, making it the most mature implementation. Wallets like Electrum, Sparrow, and Specter provide excellent user experiences.
The main limitation is that all keyholders need compatible wallet software to sign transactions. You can’t mix an Electrum key with a BlueWallet key in the same multisig setup without careful coordination.
Bitcoin multisig works at the protocol level, not through smart contracts. This makes it more secure but less flexible than Ethereum implementations.
Ethereum and EVM chains
Ethereum multisig relies on smart contracts, with Safe being the dominant platform. This approach offers more flexibility, including the ability to add or remove keyholders and change signature thresholds without creating a new wallet.
The tradeoff is smart contract risk. While Safe has been audited extensively and secured billions in assets, it’s still software that could theoretically contain bugs. Understanding what happens when you approve a smart contract helps you evaluate these risks properly.
Gas costs for multisig transactions on Ethereum can be significant during network congestion. Deploying the initial multisig contract alone might cost $50-200 in gas fees.
Other chains
Solana, Cardano, and other chains offer varying levels of multisig support. Research carefully before committing significant funds to less-proven implementations.
Some chains advertise multisig capabilities but only through third-party services rather than native protocol support. This introduces additional trust assumptions.
Alternatives to consider before choosing multisig
Multisig solves specific problems, but other approaches might better fit your situation.
Shamir’s Secret Sharing
This cryptographic technique splits a single private key into multiple shares, requiring a threshold of shares to reconstruct the original key. A 2-of-3 Shamir backup means any two shares can recover your key, but one share alone reveals nothing.
The advantage over multisig is simplicity. You use a standard wallet address, and the complexity only appears during key recovery. The disadvantage is that you must reconstruct the full key to spend funds, creating a brief moment of single-key vulnerability.
Shamir works better for backup and recovery than for ongoing transaction security. Tools like what happens if you lose your seed phrase often discuss Shamir alongside other recovery methods.
Social recovery wallets
Platforms like Argent implement social recovery, where trusted contacts can help you recover access if you lose your primary key. This provides some multisig-like security without requiring multiple signatures for every transaction.
Social recovery optimizes for convenience during normal use while maintaining security for recovery scenarios. The tradeoff is that you must trust the platform’s smart contract implementation.
Time-locked wallets
Some wallets let you set up a dead man’s switch or time-lock mechanism. If you don’t check in for six months, access automatically transfers to designated beneficiaries.
This solves inheritance problems without requiring beneficiaries to hold keys during your lifetime. The risk is that if you’re incapacitated but not deceased, funds might transfer prematurely.
Hardware wallet + passphrase
A strong passphrase added to your hardware wallet seed creates a form of 2-factor security. Someone who steals your hardware wallet and discovers your seed phrase still can’t access funds without the passphrase.
This is simpler than multisig but offers less protection against coercion (you can be forced to reveal both seed and passphrase) and doesn’t solve key loss problems (losing the passphrase means losing access).
Multisig in the broader DeFi security landscape
Multi-signature wallets represent one tool in a comprehensive security strategy. They work best when combined with other protective measures.
Your complete beginner roadmap for getting started with DeFi should include wallet security as a foundational element. Multisig fits into this foundation alongside hardware wallets, secure seed phrase storage, and careful protocol selection.
“The best security setup is one you’ll actually use consistently. A complex multisig configuration you abandon after two months provides less protection than a simpler setup you maintain properly for years.”
This quote captures an important truth about crypto security. Perfect security that’s too inconvenient gets abandoned. Good security that you maintain reliably beats perfect security that you bypass.
Consider your actual usage patterns. If you interact with DeFi protocols daily, a 3-of-5 multisig requiring coordination with four other people will frustrate you into using a less secure hot wallet for daily activities. A 2-of-3 setup where you control two keys might provide better real-world security.
The decision between hot wallets and cold wallets often intersects with multisig considerations. You might use a multisig cold wallet for long-term holdings while maintaining a single-signature hot wallet for active trading, never keeping more than 5% of your portfolio in the hot wallet.
When multisig creates more problems than it solves
Despite the security benefits, multisig isn’t appropriate for everyone. These scenarios suggest you might be better served by simpler solutions.
You hold less than $5,000 in crypto
The complexity and cost of multisig probably outweigh the benefits at this level. A single hardware wallet with a strong passphrase provides adequate security without the coordination overhead.
Multisig transaction fees and the time cost of coordinating signatures make sense when protecting substantial assets. For smaller amounts, the juice isn’t worth the squeeze.
You need frequent access
If you trade actively or interact with DeFi protocols multiple times daily, multisig friction becomes unbearable. Waiting for a second signature every time you want to provide liquidity or adjust a position kills your ability to respond to market conditions.
Active traders should use multisig for their long-term holdings vault, not for their trading stack.
Your potential keyholders are unreliable
A multisig setup is only as strong as its weakest keyholder. If you don’t have access to multiple trustworthy, technically competent people who will remain available long-term, multisig might create more risk than it prevents.
Better to use a single hardware wallet stored extremely securely than a multisig with unreliable keyholders who might lose keys or become unresponsive.
You want to maintain complete privacy
Multisig requires sharing information about your holdings with keyholders. If you need absolute privacy about your crypto assets, single-signature wallets better preserve that confidentiality.
Some people don’t want anyone, including trusted family members, to know they own cryptocurrency. Multisig fundamentally conflicts with this goal.
The practical reality of living with multisig
Theory and practice diverge significantly when you actually use multisig wallets daily. Understanding these realities helps you decide whether the commitment makes sense.
Coordination takes time
Even with the smoothest multisig setup, transactions require coordination. If you use a 2-of-3 configuration where you control two keys, you still need to access two separate devices or locations.
Need to make a payment while traveling? You might not have access to the hardware wallet sitting in your home safe. Emergency situations reveal the inconvenience of distributed keys.
Software compatibility matters
Not all wallets support all multisig standards. You might set up a Bitcoin multisig using Electrum, then later want to switch to a different wallet that doesn’t support your specific multisig configuration.
This lock-in means you need to carefully evaluate wallet longevity and support before committing. Choosing widely-supported standards over proprietary implementations reduces future migration headaches.
Keyholders need training
If your spouse holds one key in a 2-of-3 setup but doesn’t understand how to use it, you haven’t actually improved security. You’ve created a false sense of security while introducing complexity.
Each keyholder needs to successfully sign a test transaction before you trust them with real funds. This training takes time and requires patience.
Regular testing prevents disasters
You should test your multisig recovery process at least annually. Attempt to sign a transaction using different key combinations. Verify that all keyholders can still access their keys.
People discover their backup hardware wallet’s battery died, their family member moved and didn’t update their contact information, or their bank closed the safe deposit box only when they desperately need access. Regular testing catches these problems early.
Making your final decision about multisig
The choice ultimately depends on your specific circumstances, not abstract security principles.
Start by honestly assessing your holdings, your risk tolerance, and your technical comfort level. If you manage a DAO treasury or business funds, multisig is non-negotiable. If you’re protecting personal holdings, the decision requires more nuance.
Consider starting with a small multisig wallet to learn the process before moving significant funds. Set up a 2-of-3 wallet, fund it with $500, and practice the transaction workflow for a month. If the process feels manageable, scale up. If it feels unbearably cumbersome, you’ve learned this lesson cheaply.
Remember that security exists on a spectrum. A multisig wallet provides better protection than a single hardware wallet, which provides better protection than a hot wallet on your phone. But even a hot wallet beats keeping funds on an exchange.
The goal isn’t perfect security. Perfect security means never accessing your funds at all. The goal is appropriate security for your situation, implemented in a way you’ll actually maintain long-term.
Whether you choose multisig or not, understanding common mistakes beginners make when setting up their first DeFi wallet helps you avoid the most dangerous pitfalls regardless of your wallet type.
Building security that actually works for you
Multi-signature wallets represent serious security technology that solves real problems for people managing significant crypto assets or shared treasuries.
The technology isn’t magic. It won’t protect you from sending funds to the wrong address or falling for sophisticated social engineering. What it does provide is protection against single points of failure, whether that’s a stolen device, a lost key, or a compromised individual.
Your security setup should match your actual needs and capabilities. A complex multisig configuration you don’t understand or can’t maintain reliably provides less real security than a simpler approach you execute perfectly.
Start where you are. Learn the fundamentals. Test with small amounts. Scale up as your confidence and holdings grow. The crypto space rewards careful, methodical security practices and punishes overconfidence.
Whether multisig makes sense for you depends on your unique situation. But understanding what it is, how it works, and when it helps means you can make that decision from knowledge rather than guesswork.