You’re scrolling through a crypto exchange, eyeing a token that promises 100x returns. Before you hit that buy button, there’s a fundamental question you need to answer: are you buying a utility token or a security token? This distinction isn’t just semantic. It determines your legal rights, regulatory protections, and the actual value proposition of your investment.
Utility tokens provide access to products or services within a blockchain ecosystem, while security tokens represent investment contracts with profit expectations. Security tokens face strict regulatory oversight under securities laws, requiring registration and compliance. Utility tokens operate with fewer restrictions but offer no ownership rights. Understanding this difference protects investors from legal complications and helps set realistic expectations about token value and returns.
What utility tokens actually do
Utility tokens grant you access to a specific product, service, or feature within a blockchain platform. Think of them like arcade tokens or gift cards with a crypto twist.
When you hold a utility token, you’re not buying a piece of the company. You’re purchasing the ability to use something the platform offers. Filecoin lets you pay for decentralized storage. Basic Attention Token rewards you for viewing ads and lets you tip content creators. Golem tokens buy you computing power on a distributed network.
The value proposition is straightforward. You need the token to interact with the platform. As more people use the platform, demand for the token might increase. But there’s no promise of profits, no dividends, and no ownership stake.
Most importantly, utility tokens should have a functional purpose from day one or very soon after launch. If a token claims to be a utility token but has no working product, that’s a red flag worth noting.
Security tokens represent ownership and profit expectations
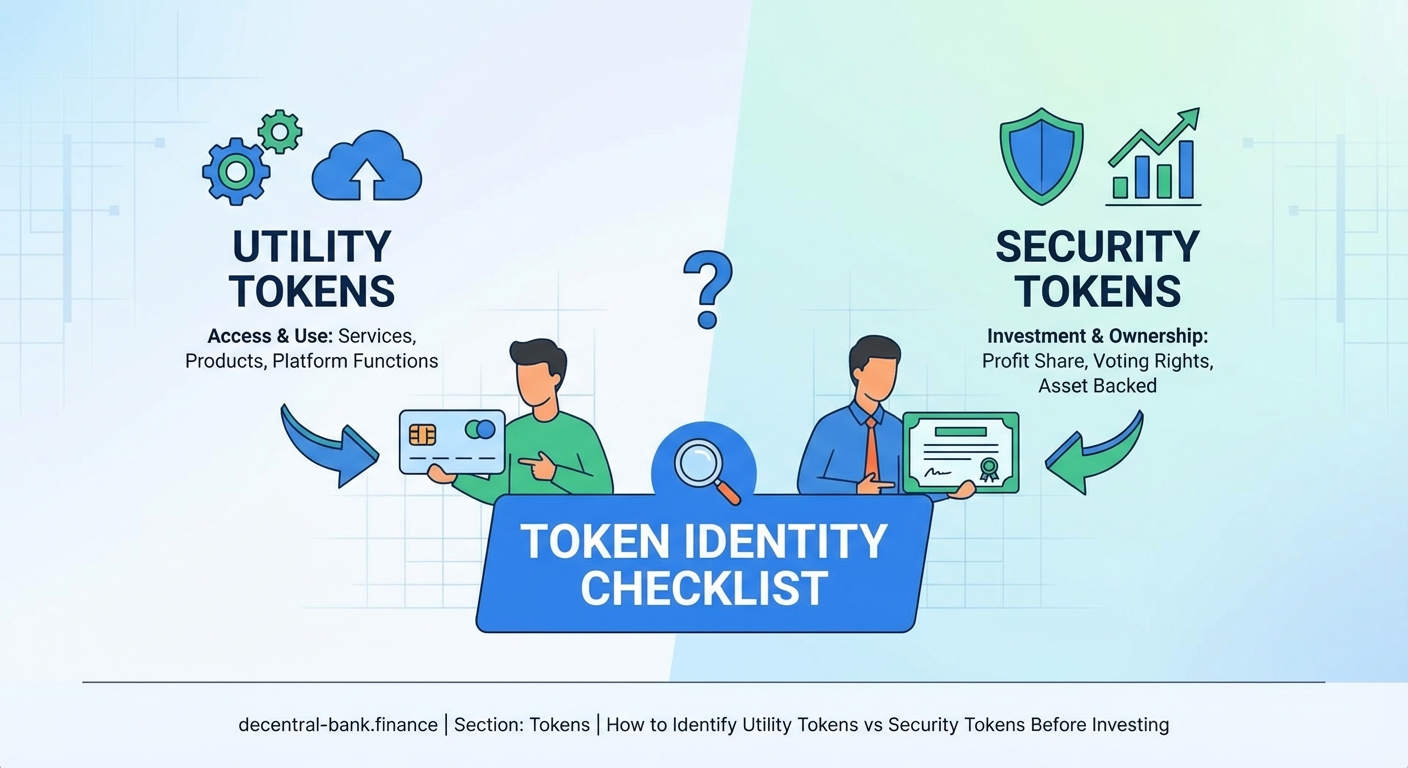
Security tokens are fundamentally different animals. They represent an investment contract where you expect profits primarily from the efforts of others.
These tokens might give you:
- Equity ownership in a company
- Rights to future revenue or profits
- Voting power on business decisions
- Claims on company assets
- Dividend payments or profit sharing
Real estate tokens that pay rental income are securities. Tokens that promise returns based on a team’s development work are securities. Tokenized shares of a startup are securities.
The defining characteristic is the expectation of profit derived from someone else’s work. You’re investing money with the hope that the project team will increase the value of your holdings.
The Howey Test determines classification
U.S. regulators use the Howey Test to determine whether something qualifies as a security. This test comes from a 1946 Supreme Court case and asks four questions:
- Is there an investment of money?
- Is there a common enterprise?
- Is there an expectation of profits?
- Do those profits come primarily from the efforts of others?
If the answer to all four questions is yes, you’re dealing with a security. This applies to tokens just as much as traditional investments.
The third and fourth questions trip up many token projects. If your marketing materials promise returns, talk about the team’s roadmap creating value, or suggest holding for future gains, regulators will likely view your token as a security.
Other countries have similar tests. The key principle remains consistent across jurisdictions: if it looks like an investment contract, it gets treated like one.
Regulatory requirements create major differences
Security tokens operate under heavy regulatory oversight. In the United States, they must either register with the SEC or qualify for an exemption. Registration requires extensive disclosures, audited financials, and ongoing reporting obligations.
Projects issuing security tokens need to:
- Comply with securities laws in every jurisdiction where they sell tokens
- Implement know-your-customer and anti-money laundering procedures
- Restrict sales to accredited investors in many cases
- Provide regular financial disclosures to token holders
- Follow trading restrictions and transfer limitations
Utility tokens face far fewer requirements, assuming they truly function as utilities and aren’t marketed as investments. They still need to follow consumer protection laws and avoid fraud, but they skip the securities registration process.
This regulatory difference explains why many projects desperately want their tokens classified as utilities. Securities compliance is expensive, time consuming, and limits your potential buyer pool.
The biggest mistake crypto investors make is ignoring regulatory classification. A token marketed as a utility but functioning as a security creates legal risk for both the issuer and potentially the holders. Always verify how regulators view a token before investing significant capital.
How marketing language reveals token type
Pay attention to how projects describe their tokens. The language tells you everything about classification, regardless of what label the team slaps on it.
Security token language includes phrases like:
- “Investment opportunity”
- “Expected returns”
- “Our team will build value”
- “Roadmap to increase token price”
- “Revenue sharing model”
- “Equity stake in the project”
Utility token language focuses on function:
- “Access to platform features”
- “Pay for services”
- “Governance rights for protocol parameters”
- “Reward for network participation”
- “Required for transactions”
If a whitepaper spends pages explaining the team’s qualifications and development plans while promising token appreciation, you’re looking at a security. If it focuses on the technical implementation and specific use cases, it’s more likely a utility.
Many projects try to have it both ways, describing utility features while winking at profit potential. This creates legal ambiguity that puts investors at risk.
Common classification mistakes investors make
| Mistake | Why It Happens | Actual Reality |
|---|---|---|
| Assuming exchange listings mean legitimacy | Exchanges list tokens before regulatory clarity | Listed tokens can still be unregistered securities |
| Believing “utility” labels at face value | Projects self-classify to avoid regulation | Actual function and marketing determine classification |
| Thinking decentralization prevents security status | Decentralization affects some factors | Sufficiently decentralized tokens may avoid security status, but most new tokens don’t qualify |
| Ignoring profit marketing if utility exists | Tokens can have utility features | Primary expectation of profit still triggers security classification |
| Assuming foreign projects avoid U.S. laws | Tokens sold to U.S. investors | U.S. securities laws apply regardless of project location |
The decentralization point deserves extra attention. Some truly decentralized protocols have tokens that started as securities but evolved into utilities. Bitcoin and Ethereum fall into this category for many regulators. But this transition requires genuine decentralization where no identifiable group controls the protocol’s success.
New token launches rarely meet this standard. The founding team typically holds significant influence over development, marketing, and token economics.
Investment risks differ by token type
Utility tokens carry functional risk. If the platform fails to attract users, your tokens become worthless regardless of the team’s efforts. You’re betting on product-market fit and adoption.
The upside potential comes from increased platform usage driving token demand. But there’s no inherent mechanism forcing value appreciation. A successful platform might even reduce token prices if it improves efficiency.
Security tokens carry business risk. You’re investing in the team’s ability to execute their business plan and generate returns. This aligns more closely with traditional investing.
Security tokens should offer better investor protections through regulatory oversight, disclosure requirements, and legal recourse. But they also limit liquidity through transfer restrictions and accredited investor requirements.
Unregistered securities carry the worst risk profile. If regulators determine a token is an unregistered security, the project faces enforcement actions, exchanges delist the token, and holders may struggle to sell. Some investors have even faced tax complications from holding unregistered securities.
Practical steps to classify tokens before investing
Start by reading the project’s whitepaper and marketing materials with a critical eye. Look for profit promises and investment language versus functional descriptions.
Check regulatory statements from the SEC, FCA, or relevant authorities in your jurisdiction. Many have issued guidance on specific tokens or general classification principles.
Review how the token functions in practice. Can you actually use it for something today? Does the platform require it, or is it optional? Are people using it for utility or just speculating?
Examine the token distribution and vesting schedules. Large team allocations with long vesting periods suggest the team expects their future work to drive value, pointing toward security classification.
Consider who can buy the token. Restrictions to accredited investors signal the project treats it as a security. Open sales to anyone suggest utility classification, though this alone doesn’t determine status.
Research whether the project has taken steps toward securities compliance. Registered offerings, Regulation D exemptions, or Regulation A+ filings indicate security token status.
Real examples illustrate the differences
Filecoin operates as a utility token. You pay FIL to store data on the network or earn it by providing storage. The token has a clear functional purpose within a working product.
Many initial coin offerings from 2017 were actually unregistered securities. Projects raised money by promising future platform development would increase token value. Teams controlled all development efforts. Investors expected profits from the team’s work. Classic securities that should have registered.
tZERO issued a registered security token representing equity in the company. Investors received actual ownership rights, profit sharing, and voting power. The token complied with securities laws from the start.
Uniswap’s UNI token sits in a gray area. It provides governance rights over protocol parameters but was initially distributed freely rather than sold. The decentralized nature and lack of direct profit mechanism push it toward utility classification, though reasonable people disagree.
These examples show classification isn’t always black and white. But the core distinction between access tokens and investment contracts remains clear in most cases.
Why this matters for your investment strategy
Understanding token classification shapes your entire investment approach. Security tokens require evaluating the team, business model, competitive landscape, and financial projections, just like traditional investments.
Utility tokens demand different analysis. You need to assess product-market fit, adoption metrics, network effects, and whether the token economics actually require the token. Many platforms could function without their token, making it purely speculative.
Regulatory classification also affects your holding strategy. Security tokens may have transfer restrictions, vesting periods, or accredited investor requirements that limit liquidity. Utility tokens typically trade more freely but offer no legal protections if things go wrong.
Tax treatment differs too. Securities have well-established tax rules. Utility tokens exist in murkier territory where guidance continues evolving.
Your risk tolerance should align with token type. If you want regulatory protections and traditional investment characteristics, focus on properly registered security tokens. If you’re comfortable with higher risk in exchange for potential higher returns and fewer restrictions, utility tokens might fit better.
Making informed decisions in crypto markets
Token classification isn’t just regulatory paperwork. It reveals the fundamental nature of what you’re buying and the realistic expectations you should hold.
Security tokens are investments in a team and business model. Utility tokens are bets on product adoption and network effects. Confusing the two leads to mismatched expectations and poor investment decisions.
Before you invest in any token, take the time to understand what you’re actually buying. Read beyond the marketing hype. Apply the Howey Test yourself. Check regulatory statements. Verify actual utility versus promised returns.
The crypto space moves fast, but this fundamental distinction remains constant. Knowing whether you’re buying utility or security protects your capital and helps you build a more thoughtful investment strategy.
Leave a Reply